The declining costs of single-board computers has made serious computing power available for even the most trivial of tasks. It’s easy enough to slap a Raspberry Pi onto almost anything for nearly the same cost as a powerful 32-bit microcontroller platform, but this takes some of the fun out of projects for a few of us. Looking to get into the weeds can be a challenge as well, as [Michal Zalewski] demonstrates in this audio playback device he built from a simple 8-bit microcontroller.
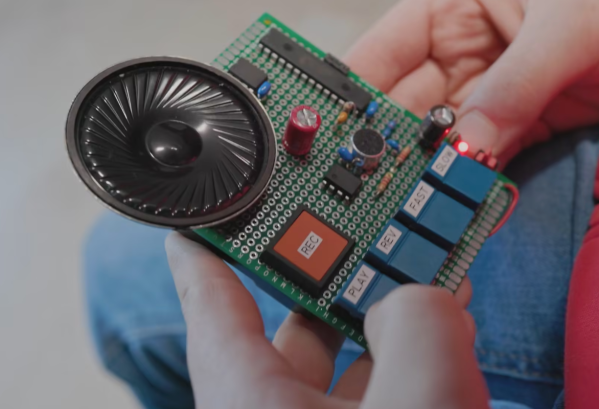
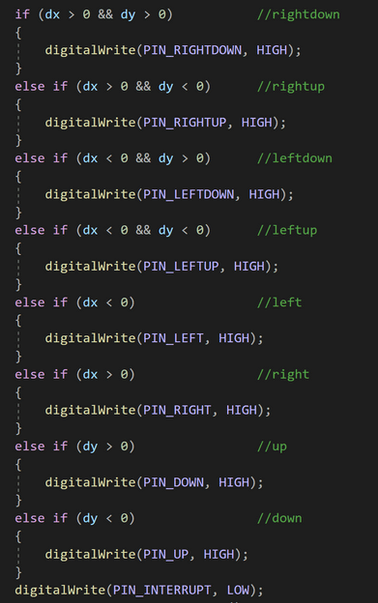
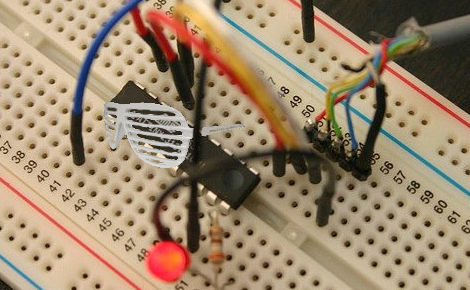
The small toy takes audio input from a microphone through an op-amp and feeds this signal to an ADC within the AVR128DA28 microcontroller. The data is then stored on a separate memory chip ready to be played back through another op-amp paired with a speaker. This is where being familiar with the inner workings of the microcontroller comes in handy. By manipulating the interrupt routines in specific ways, the audio stored in memory can be played back at various speeds.
[Michal] intended this build to be a toy for one of his younger relatives, and for the price of a few ICs and buttons it does a pretty good job of turning a regular voice into a chipmunk voice like some commercial children’s toys some of us might remember. If the design aesthetics of this gadget look familiar, you may be thinking of his minimalist gaming device which we recently featured.