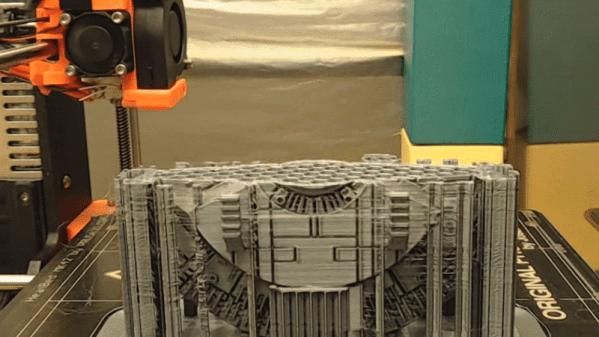
Most time-lapse videos of 3D prints show a steadily growing print with a crazy blur of machine movement everywhere else. This is because an image is captured at a regular time interval, regardless of what’s physically going on with the machine. But what if images were captured at consistent machine positions instead? [FormerLurker]’s Octolapse plugin for OctoPrint came out of beta recently and does exactly that, and the results are striking. Because OctoPrint knows where a 3D printer’s print head is at all times, it’s possible for a plugin to use this information to create time-lapse videos where the print head position is consistent instead of a crazy blur, or even have the print head absent from the shot altogether.
[FormerLurker] had originally created stabilized time lapses by hand editing G-code, which had great results but was inefficient and time-consuming. This plugin is the result of his work at automating and enhancing the process, and is also his first serious open source programming project. We’ve covered upgrading a 3D printer with OctoPrint before, and the plugins functionality of OctoPrint means features can be added independently from the core system, which itself largely remains a one-woman effort by creator and maintainer [Gina Häußge].