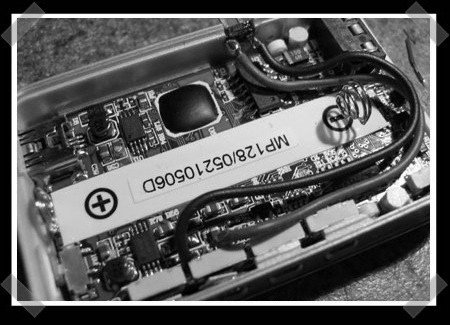
Reader [Kelly Regan] flies large scale RC planes, but would often need someone call out flight sequences while rehearsing. Not wanting to impose on fellow club members, [Kelly] built a sequencer caller from a cheap MP3 player. It just required extending the FWD key to a pin header. Those pins are connected to a custom switch on the back of the controller. Each maneuver is recorded with 30 seconds of padding and then added to a playlist. Once the maneuver is complete, a quick press of the button moves on to the next track. It’s always nice to see people building devices that the consumer electronics industry probably wouldn’t.
Day: August 26, 2008
Key Features Cut Out Of Android API

Google has decided that its initial release of the Android SDK will not include formal Bluetooth support or Google Talk. Bluetooth headsets will still work, but developers will not have access to the Bluetooth portion of the API. Google’s security researchers have announced that Google Talk was left out because of multiple security concerns. Bluetooth, on the other hand, was left out because the development team ran out of time.
Out of these two features, we think users are going to be most disappointed by the omission of Google Talk. Chatting has become one of the most useful features of new smart phones. The ability to just chat instead of sending a text message is one of the main attractions to phones like the iPhone, which has support for AIM.
[photo: dreamside]
IBM Sees Influx In Zero-day Exploits
IBM’s X-Force security team has released a mid-year report(PDF) stating that the number of zero-day exploits is growing at an alarming rate. For those of you unfamiliar with the term, a zero-day exploit is a program that is created and implemented within 24 hours of the disclosure of a security flaw. These exploits usually affect users before they even know the vulnerability exists and long before a patch is made available. The researchers also found that many of these exploits were targeted at browser plug-ins, which most users utilize on a daily basis.
[Kris Lamb], X-Force operations manager, is blaming the problem on a lack of a unified process for disclosing vulnerabilities. He also claims that the long-held practice of publishing example code of vulnerabilities should be frowned upon.
[via Liquidmatrix]
Coyote-1 Guitar Pedal Available Now

OpenStomp’s Coyote-1 is now available for $349. The guitar effects pedal lets users design and upload their own effects to the device. It has two stomp switches with LEDs, an LCD display, and four user assignable knobs. The back has 1/4″ in/out and one selectable 1/4″. It also features NTSC composite out, a headphone jack, mini-USB for uploading, and an RJ11 I2C bus for expansion. The processor is a Parallax Propeller Chip. While the OS on the pedal is open source, the hardware design and effect design software are not. You can check out the source and product manual on their forum. If you’re more interested in breadboarding hardware, you might like the Beavis Board we covered earlier.
[via Create Digital Music]
Large Hadron Collider User Manual Online
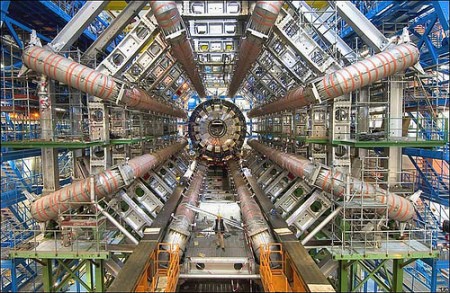
If you’ve got a few hours (or weeks) of spare time, you could learn how to run the Large Hadron Collider, located at CERN in Switzerland. CERN published the full technical details of the collider and detectors online, and anyone with some curiosity and patience can read all 1,589 pages. Tell us if you got through all of it, and if you’re planning to make your own particle accelerator.
[via MetaFilter]
Customers Make VoIP Calls On American Airlines Flights

Less than a week after American Airlines introduced in-flight internet, hackers have already figured out how to use the system to make VoIP calls in a few easy steps with Phweet, a Twitter application. While the network blocks most VoIP services, Phweet can connect two people using a Flash app. Aircell, the company responsible for the system, is aware of the oversight, but it remains to be seen whether this little loophole will be fixed in a timely manner. Meanwhile, we encourage those of you who do fly on American Airlines to avoid making those phone calls; your neighbor would probably appreciate it.
[via Digg]










