While browsing AliExpress from his digital basement, [Adrian Black] stumbled upon what seemed like a brand-new mainboard for a CRT television set. He decided to take a gamble and ordered one. It finally arrived, and was indeed a brand new product from 2023.
DIGITAL MAIN BOARD OF TV, Work ath [sic] HONGXUN products with the care and precision of a sculptor in each step, wonderful have no limits
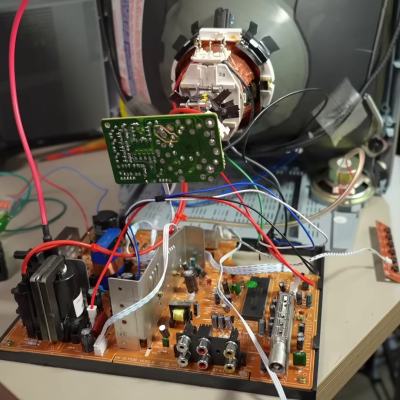
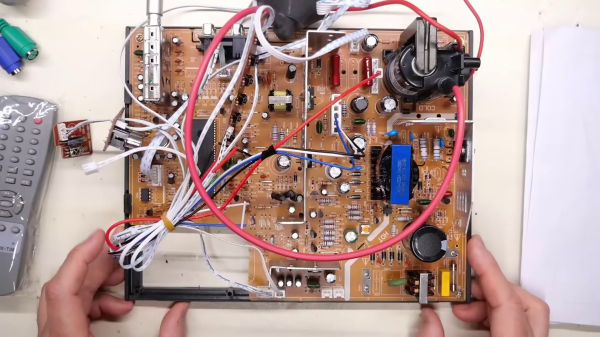
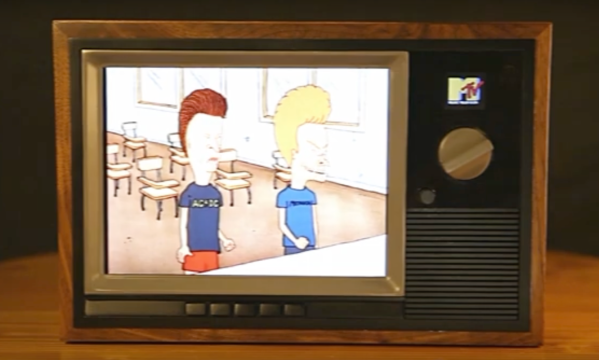
Dubious marketing descriptions like “High Definition Digital Color TV Driver Board” aside, this turned out to be a fairly well-designed analog TV board. [Adrian] pulls a 20-year-old Magnavox ( Philips ) color television set from storage and begins the transplant operation. One interesting observation is the Magnavox board has almost the same layout as the new board, except for the orientation of the sections. The new CRT neck board had a different connector than the Magnavox set, but was designed to accept multiple sized sockets. [Adrian] just removed the new socket and replaced it with one from the old set. The mechanical issues were a bit more complicated, but nothing that a Dremel tool and a bit of hot glue can’t fix. The 220 VAC power supply was eventually modified to accept 110 VAC, which also enabled him to reconnect the degaussing coil.
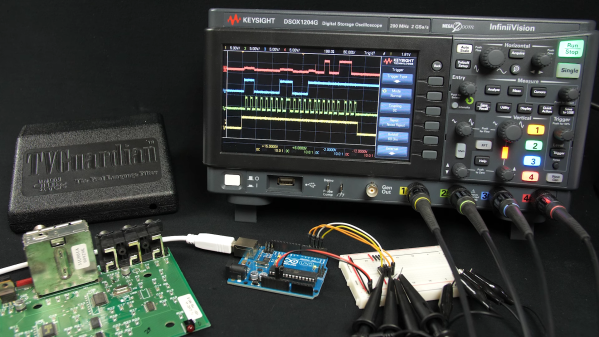
[Adrian] has collected some relevant documentation in this GitHub repository, including schematics. Why bother with this at all? Well, until now, he didn’t have any way to test / view PAL RF signals in his lab. He was gambling on the new mainboard having a PAL tuner. It does, but as an unadvertised bonus, it supports NTSC and SECAM as well — but still not “HD digital color TV”, as far as we know. If you want a multi-standard TV in your lab, this solution may be worth considering. It appears there is still a market somewhere for new CRT televisions. If you have any background on this, please let us know down below in the comments.
Continue reading “New Motherboard Improves Old CRT Television”