It was around the year 1590 when mankind figured out how to use optical lenses to bring into sight things smaller than the natural eye can observe. With the invention of the microscope, a new and unexplored world was discovered. It will likely be of great surprise to the reader that scientists of the time did not believe that within this new microscopic realm lay the source of sickness and disease. Most would still hold on to a belief of what was known as Miasma theory, which dates back to the Roman Empire. This theory states that the source of disease was contaminated air through decomposing organic materials. It wouldn’t be until the 1850’s that a man by the name of Louis Pasteur, from whom we get “pasteurization”, would promote Germ Theory into the spotlight of the sciences.
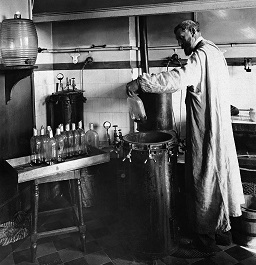
Pasteur, considered by many as the father of microbiology, would go on to assist fellow biologist Charles Chameberland in the invention of the aptly named Pasteur Chamberland filter — a porcelain filter with a pore size between 100 and 1000 nanometers. This was small enough to filter out the microscopic bacteria and cells known at that time from a liquid suspension, leaving behind a supply of uncontaminated water. But like so many other early scientific instrumentation inventions it would lead to the discovery of something unexpected. In this case, a world far smaller than 100 nanometers… and add yet another dimension to the ever-shrinking world of the microscopic.
This is when we began to learn about viruses.

 University of Michigan have figured out a way to
University of Michigan have figured out a way to