They say time is money, but if that’s true, money must also be time. It’s all figurative, of course, but in the case of this NTP server heater powered by Bitcoin mining dongles, money actually does become time.
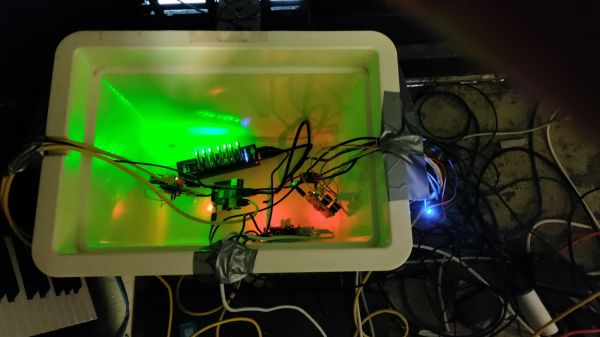
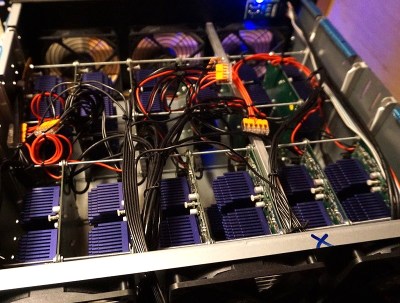
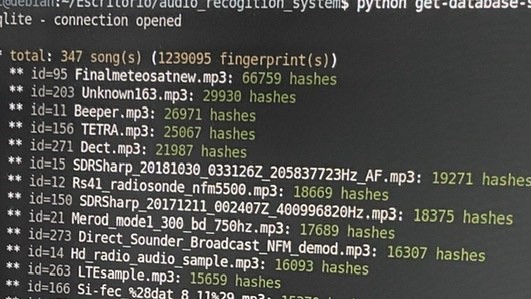
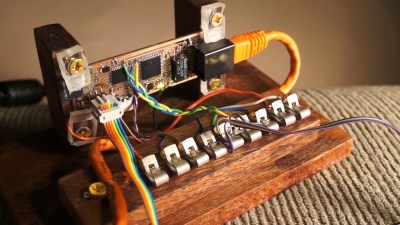
This is an example of the lengths to which Network Time Protocol aficionados will go in search of slightly better performance from their NTP servers. [Folkert van Heusden], having heard that thermal stability keeps NTP servers happy, used a picnic cooler as an environmental chamber for his Pi- and GPS-based NTP rig. Heat is added to the chamber thanks to seven Block Erupter ASIC miner dongles, which are turned on by a Python script when a microcontroller sends an MQTT message that the temperature has dropped below the setpoint.
Each dongle produces about 2.5 Watts of heat when it’s working, making them pretty effective heaters. Alas, heat is all they produce at the moment — [Folkert] just has them working on the same hash over and over. He does say that he has plans to let the miners do useful work at some point, not so much for profit but to at least help out the network a bit.
This seems like a bit of a long way around to solve this problem, but since the mining dongles are basically obsolete now — we talked about them way back in 2013 — it has a nice hacky feeling to it that we appreciate.