We get results! Well, sort of. You may recall that in this space last week we discussed Ford’s plans to exclude AM reception on the infotainment systems of certain of their cars starting in 2024. We decried the decision, not for the loss of the sweet, sweet content that AM stations tend to carry — although we always enjoyed “Traffic on the 8s” back in our dismal days of daily commuting — but rather as a safety concern, because AM radio can reach almost the entire US population with emergency information using just 75 stations. To our way of thinking, this makes AM radio critical infrastructure, and eliminating it from motor vehicles is likely to have unintended consequences. Now it seems like there’s some agreement with that position, as former administrators of FEMA (Federal Emergency Management Administration; and no, not FEDRA) have gotten together to warn about the dangers of deleting AM from cars. Manufacturers seem to be leaning into the excuse that EVs emit a lot of radio frequency interference, rendering static-sensitive AM receivers less useful than other, more profitable less susceptible modes, like digital satellite radio. That seems like a red herring to us, but then again, the most advanced infotainment option in any car we’ve ever owned is a CD player, so it’s hard for us to judge.
Hackaday Columns4720 Articles
This excellent content from the Hackaday writing crew highlights recurring topics and popular series like Linux-Fu, 3D-Printering, Hackaday Links, This Week in Security, Inputs of Interest, Profiles in Science, Retrotechtacular, Ask Hackaday, Teardowns, Reviews, and many more.
Study Hacker History, And Update It
Looking through past hacks is a great source of inspiration. This week, we saw [Russ Maschmeyer] re-visiting a classic hack by [Jonny Lee] that made use of a Wiimote’s IR camera to fake 3D, or at least provide a compelling parallax effect that’ll fool your brain, without any expensive custom hardware.
![]() [Lee]’s original demo was stunning, and that alone is reason to revisit it. Using the Wiimote as the webcam was inspired back in 2007, because it meant that there was no hard computer vision work to be done in estimating the viewer’s position – the camera only sees IR LEDs anyway. The tradeoff is that you had to wear two IR LEDs on your head, calibrate it just right, and that only the person with the headset on gets the illusion just right.
[Lee]’s original demo was stunning, and that alone is reason to revisit it. Using the Wiimote as the webcam was inspired back in 2007, because it meant that there was no hard computer vision work to be done in estimating the viewer’s position – the camera only sees IR LEDs anyway. The tradeoff is that you had to wear two IR LEDs on your head, calibrate it just right, and that only the person with the headset on gets the illusion just right.
This is why re-visiting the past can be fruitful. As [Russ] discovered, computing power is so plentiful these days that you could do face/eye position estimation with a normal webcam easier than you could source an old Wiimote. Indeed, he’s getting the positioning so accurate that he’s worried about to which eye he’s projecting the illusion. Clearly, it’s time for a revamp.
So here’s the formula: find a brilliant old hack, and notice if it was hampered by the state of technology back when it was done. Update this using modern conveniences, and voila! You might just find that you can take the idea further, simply because you have more tools in your toolbox. Nothing wrong with standing on the shoulders of giants.
But beware! Time isn’t sitting still for you either. As soon as you make your killer 3D vision hack, VR goggles will become cheap and ubiquitous. So get it done today, before your hack becomes inspiration for the future.
Hackaday Podcast 210: Living In The Future, Flipper Mayhem, And Samsung Moons The World
Editor-in-Chief Elliot Williams is joined this week by newly minted Development Editor (and definitely not brother) Al Williams to bring you the weekly highlights from our little corner of the Internet. Between the rapidly approaching deadline for the Low-Power Challenge to Samsung creating a fake Moon with artificial intelligence, there’s plenty in the news to get this episode started. From there, the Williams plural discuss using a webcam for cheap virtual reality thrills, an impressive expansion for the Flipper Zero, and whether or not finding a bug in the Nintendo DSi browser counts as retrocomputing. Stick around to hear about the fascinating work Joshua Vasquez has been doing with DIY light guide plates, and Arya Voronova’s deep-dive into PCI-Express.
Check out the links below if you want to follow along, and as always, tell us what you think about this episode in the comments!
This Week In Security: Kali Purple, Malicious Notifications, And Cybersecurity Strategy
After a one-week hiatus, we’re back. It’s been a busy couple weeks, and up first is the release of Kali Purple. This new tool from Kali Linux is billed as an SOC-in-a-box, that follows the NIST CSF structure. That is a veritable alphabet soup of abbreviated jargon, so let’s break this down a bit. First up, SOC IAB or SOC-in-a-box is integrated software for a Security Operation Center. It’s intrusion detection, intrusion prevention, data analysis, automated system accounting and vulnerability scanning, and more. Think a control room with multiple monitors showing graphs based on current traffic, a list of protected machines, and log analysis on demand.
NIST CSF is guidance published by the National Institute of Standards and Technology, a US government agency that does quite a bit of the formal ratification of cryptography and other security standards. CSF is the CyberSecurity Framework, which among other things, breaks cybersecurity into five tasks: identify, protect, detect, respond, and recover. The framework doesn’t map perfectly to the complexities of security, but it’s what we have to work with, and Kali Purple is tailor-made for that framework.
Putting that aside, what Purple really gives you is a set of defensive and analytical tools that rival the offensive tools in the main Kali distro. Suricata, Arkime, Elastic, and more are easily deployed. The one trick that really seems to be missing is the ability to deploy Kali Purple as the edge router/firewall. The Purple deployment docs suggest an OPNSense deployment for the purpose. Regardless, it’s sure to be worthwhile to watch the ongoing development of Kali Purple.
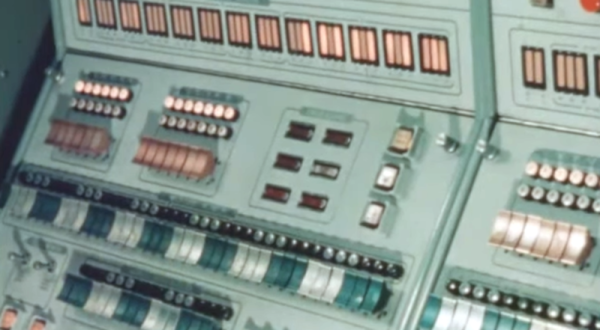
Retrotechtacular: Military Graphics In The 1960s
While you might think the military doesn’t have a sense of humor with names. Take the AN/MSQ-19 “automated tactical operations central” for example. (Video, embedded below.) But then, when you find out that the truck-sized computer at the heart of it was MOBIDIC — yes, that’s pronounced Moby Dick — you know someone had a good chuckle somewhere. The video below was a promotional video from the early 1960s, and although it shows the unit in operation, it was most likely a mockup and not fully functional.
The MOBIDIC program ran from 1960-1964 and cost a whopping $25 million in 1960-era money. In 1964, testing revealed the system was too unwieldy, requiring at least five tractor-trailers, eight generators, portable buildings, and several large trucks to move around.
Continue reading “Retrotechtacular: Military Graphics In The 1960s”
Hackaday Berlin: The Badge, Workshops, And Lightning Talks
Hackaday Berlin is just under two weeks away, and we’ve got news times three! If you don’t already have tickets, there are still a few left, so grab them while they’re hot. We’ll be rolling out the final full schedule soon, but definitely plan on attending a pre-party Friday night the 24th, followed by a solid 14-hour day of hacking, talks, and music on Saturday the 25th, and then a mellow Bring-a-Hack brunch with impromptu demos, workshops, and whatever else on Sunday from 10:30 until 14:00.
The Badge Round Two
Many Europeans weren’t able to make the flight to Supercon, so here’s your chance to get hands on Voja Antonic’s superb down-to-the-metal computer trainer-slash-retrocomputer on this side of the Atlantic. It’s been re-skinned for Berlin, with a couple hardware tweaks because nobody can leave a board revision alone, but it’s 100% compatible with the badge that took Supercon 2022 by storm.
If you want to read more about it, you should. We loved it, and so did the crowd. One of the coolest badge hardware hacks was a “punchcard” reader, but there was also a lot of work on the software side as well, and we got pull requests for most of the cool demos. If you’re coming, and if you’d like to start your badge hacking a bit early, you could start your research now.
We’ll have a Badge Hacking Ceremony Saturday night, so you can show off whatever you made. It’s lots of fun. Continue reading “Hackaday Berlin: The Badge, Workshops, And Lightning Talks”
Supercon 2022: Irak Mayer Builds Self-Sustainable Outdoor IoT Devices
[Irak Mayer] has been exploring IoT applications for use with remote monitoring of irrigation control systems. As you would expect, the biggest challenges for moving data from the middle of a field to the home or office are with connectivity and power. Obviously, the further away from urbanization you get, the sparser both these aspects become, and the greater the challenge.
[Irak] solves his connectivity problem by assuming there is some WiFi network within range, building a system around the Blues Wireless WiFi note card. Substituting their cellular card would be an option for applications out of WiFi range, but presumably without changing too much on the system and software side of things. Leveraging the Adafruit FeatherWing INA219, which is a bidirectional current sensor with an I2C interface, for both the power generation and system consumption measurements. For control, [Irak] is using an Adafruit ESP32 board, but says little more about the hardware. On the software side, [Irak] is using the Blues Wireless NoteHub for the initial connection, which then routes the collected data onto the Adafruit IoT platform for collation purposes. The final part of the hardware is a LiPo battery which is on standby to soak up any excess power available from the energy harvesting. This is monitored by an LC709203f battery fuel gauge.
Continue reading “Supercon 2022: Irak Mayer Builds Self-Sustainable Outdoor IoT Devices”