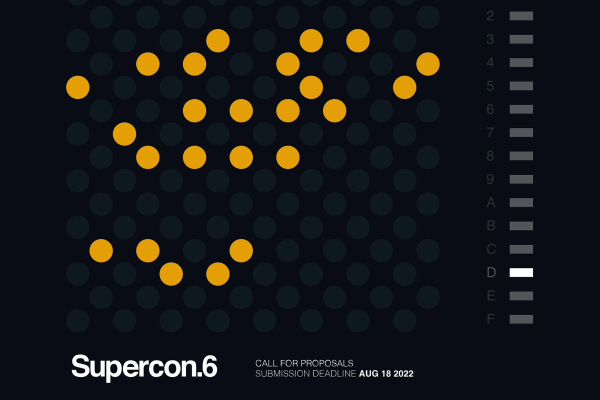
After two years in remote mode, we’re very excited to announce that this year’s Hackaday Supercon will be coming back, live! Join us Nov. 4th, 5th, and 6th in sunny Pasadena, CA for three days of hacks, talks, and socializing with the Hackaday community. And we’d love to see and hear in person what you’ve been up to for the last two years – so start brainstorming what you’re going to talk about now and fill out the call for proposals.
Supercon is On!
We’ll be starting off on Friday Nov. 4th with early-bird registration, a mellow afternoon of badge-hacking and workshops, and a party to kick off the con. Saturday and Sunday will be the full enchilada: two tracks of talks, hacking stations and food set up in the alley, and workshops aplenty. (Just thinking about hacking in the alley and sharing tacos afterward again brings a tear of joy to my eye.) We’ll close up Sunday night with the 2022 Hackaday Prize Awards and a chance to demo the weekend’s badge hacking on stage.
 If you haven’t ever been to a Supercon before, it’s Hackaday in real life. People bring hacks to show and share, projects to work on, and their ideas that are too big to fit in the overhead compartment anyway. The crowd is awesome. There are seasoned pros, famous YouTubers, and brand-new hackers to boot. But yet it’s not overwhelming – Supercon is too big to fit in your living room, but it’s nonetheless cozy. The folks in attendance are all fantastic and you’ll stumble into the most awesome conversations.
If you haven’t ever been to a Supercon before, it’s Hackaday in real life. People bring hacks to show and share, projects to work on, and their ideas that are too big to fit in the overhead compartment anyway. The crowd is awesome. There are seasoned pros, famous YouTubers, and brand-new hackers to boot. But yet it’s not overwhelming – Supercon is too big to fit in your living room, but it’s nonetheless cozy. The folks in attendance are all fantastic and you’ll stumble into the most awesome conversations.
It’s a weekend you don’t want to miss, so start figuring out how you’re going to get to Pasadena now.
We’ll be putting tickets on sale soon, and while we can’t see into the future, they have sold out every year, so keep your eyes on Hackaday to get yours. And of course, speakers don’t need no stinking tickets. Continue reading “The 2022 Hackaday Supercon Is On! And The Call For Proposals Is Open”