A devastating diagnosis for a young child is every parent’s worst nightmare. All too often there’s nothing that can be done, but occasionally there’s a window of opportunity to make things better for the child, even if we can’t offer a cure. In that case even a simple hack, like a rapid response stairwell light to help deal with night-blindness, can make a real difference.
[Becca] isn’t yet a year old, but she and her parents carry a heavy burden. She was born with Usher Syndrome, an extremely rare genetic disease that affects hearing and vision to different degrees. In [Becca]’s case, she was born profoundly deaf and will likely lose her sight by the time she’s 10 or so. Her dad [Jake] realized that the soon-to-be-toddler was at risk due to a dark stairwell and the night-blindness that accompanies Usher, so he came up with a simple tech solution to the problem.
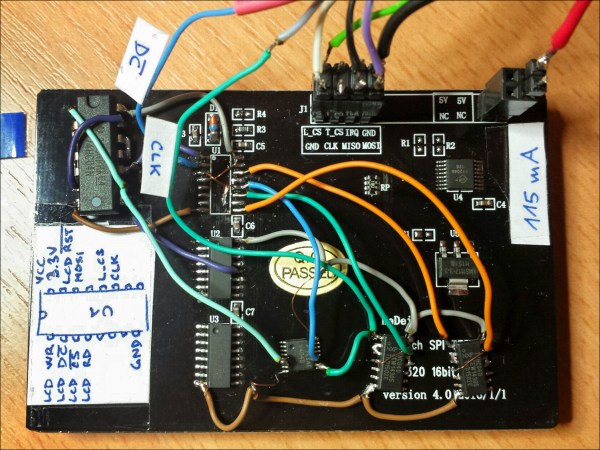
He chose Philips Hue LED light strips to run up the stringer of the stairs controlled by a Raspberry Pi. Originally he planned to use IFTTT for the job but the latency resulted in the light not switching on fast enough. He ended up using a simple PIR motion sensor which the Pi monitors and then uses the Hue API to control the light. This will no doubt give him a platform for future capabilities to help [Becca].
We’ve covered a few builds where parents have hacked solutions for their kids, like this custom media center for the builder’s autistic son. We suspect [Jake] has a few more tricks up his sleeve to help [Becca], and we’re looking forward to seeing how she does.



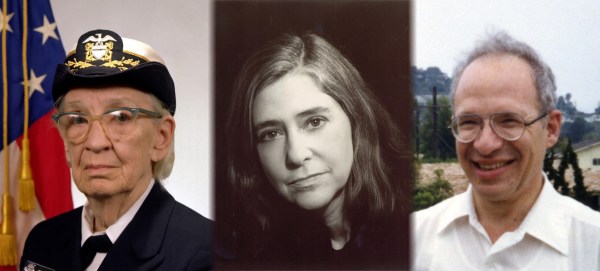

 As Director of Apollo Flight Computer Programming,
As Director of Apollo Flight Computer Programming,  Physicist
Physicist