The saying “time and tide wait for no man” is usually used as a verbal kick in the pants, a reminder that sometimes an opportunity must be seized quickly before it passes by. But it can also be interpreted as a warning about the perpetual march of time and how it impacts the world around us. In that case, we would do well to add cellular technology to the list of proverbial things that wait for no one. Do you need 5G? No. Do you want it? Probably not. But it’s here, so be a good consumer and dump all your 4G hardware in the name of technical progress.
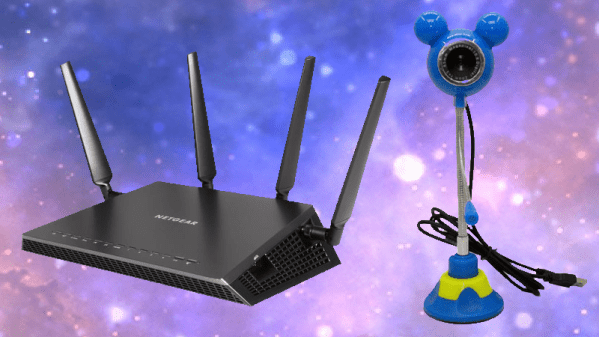
This line of logic may explain how the Verizon-branded Netgear AC791L 4G “Jetpack” hotspot you see here, despite being in perfect working order, found itself in the trash. The onset of 5G must have been particularly quick for the previous owner, since they didn’t even bother to wipe their configuration information from the device. In the name of journalistic integrity I won’t divulge the previous owner’s identity; but I will say that their endearing choice of WPA2 key, iluvphysics, makes for a nice fit with our publication.
A quick check of eBay shows these devices, and ones like it, are in ample supply. At the time of this writing, there were more than 1,500 auctions matching the search term “Verizon jetpack”, with most of them going for between $20 and $50 USD. We like cheap and easily obtainable gadgets that can be hacked, but is there anything inside one of these hotspots that we can actually use? Let’s find out.
Continue reading “Teardown: Verizon AC791L Jetpack 4G Mobile Hotspot”