Drawn along in the wake of the 3d printing/home shop revolution has been the accessibility of traditional subtractive CNC equipment, especially routers and mills. Speaking of, want a desktop mill? Try a Bantam Tools (née Othermachine) Desktop Milling Machine or a Carvey or a Carbide 3D Nomad. Tiny but many-axis general purpose mill? Maybe a Pocket NC. Router for the shop? Perhaps a Shapeoko, or an X-Carve, or a ShopBot, or a… you get the picture. [Rundong]’s MatchSticks device is a CNC tool for the shop and it might be classified as a milling machine, but it doesn’t quite work the way a more traditional machine tool does. It computer controls the woodworker too.

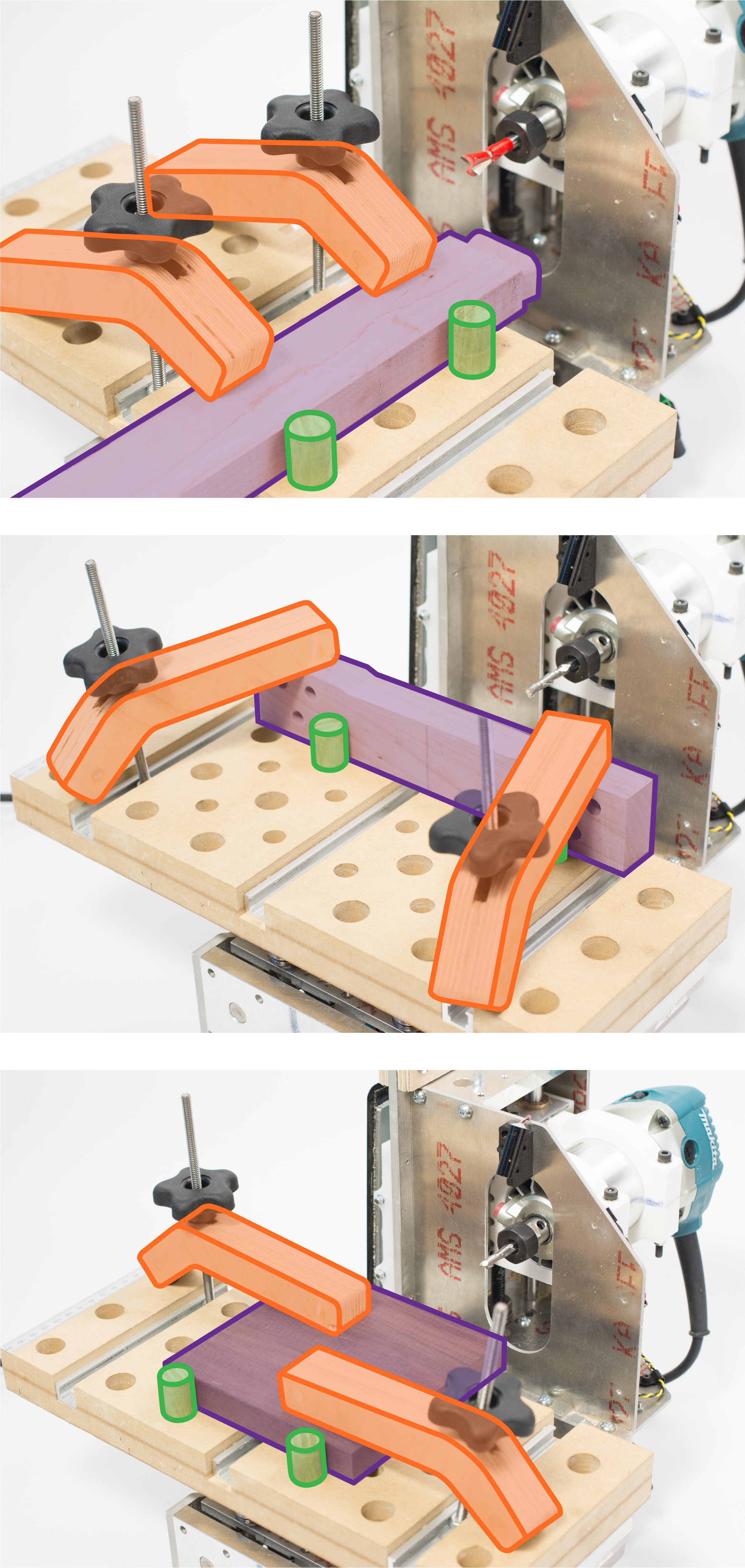
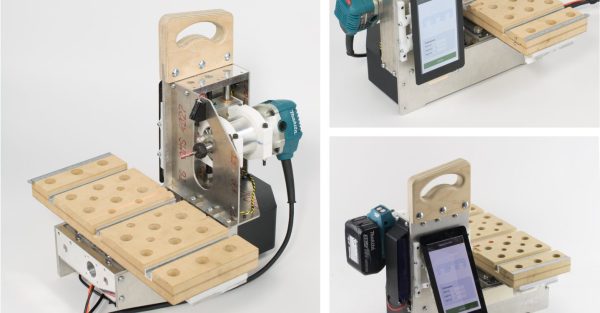
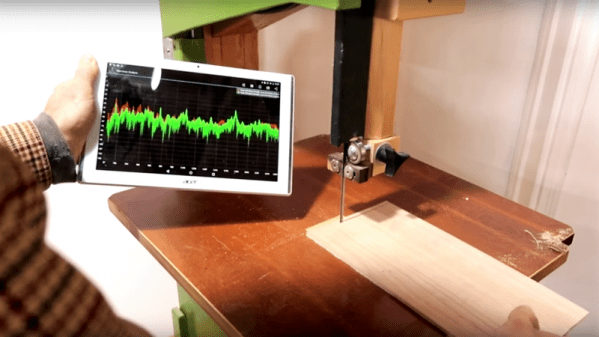
At a glance MatchSticks probably looks most similar to a Pocket NC with a big Makita router sticking out the side. There’s an obvious X-axis spoilboard with holes for fixturing material, mounted to a gantry for Z-axis travel. Below the big friendly handle on top is the router attached to its own Y-axis carriage. The only oddity might be the tablet bolted to the other side. And come to think of it the surprisingly small size for such an overbuilt machine. What would it be useful for? MatchSticks doesn’t work by processing an entire piece of stock at once (that what you’re for, adaptable human woodworker) it’s really a tool for doing the complex part of the job – joinery – and explaining to the human how to do the rest.
 The full MatchSticks creation flow goes like this:
The full MatchSticks creation flow goes like this:
- Choose a design to make on the included interface and specify the parameters you want (size, etc).
- The MatchSticks tool will suggest what material stocks you need, and then ask you to cut them to size and prepare them using other tools.
- For any parts which require CNC work the tool will help guide the user to fixture the stock to its bed, then do the cutting itself.
- Once everything is ready for final assembly the MatchSticks will once again provide friendly instructions for where to pound the mallet.
In this way [rundong], [sarah], [jeremy], [ethan], and [eric] were able to build a much smaller machine tool without sacrificing much practical functionality. It’s almost software-like in it’s focus on a singular purpose. Why reinvent what the table saw can do when the user probably already has access to a table saw that will cut stock better? MatchSticks is an entire machine bent around one goal, making the hard stuff easier.
It’s worth noting that MatchSticks was designed as an exploration into computer/human interaction for the ACM Conference on Human Factors in Computing Systems so it’s not a commercial product quite yet (we’re eagerly waiting!). For a much more in depth look at the project and its goals and learnings the full research paper is available here. Their intro video is down after the break.
Thanks [ethan] for the tip!
Continue reading “A CNC Woodworking Tool That Does The Hard Parts”

 submitted to
submitted to 

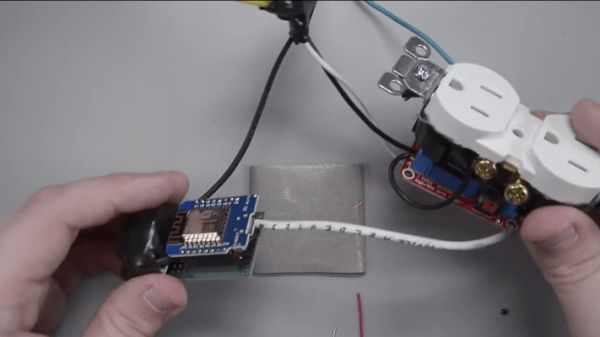

 The CNC router in question is the popular Sienci, and the 3D-printed brackets for the photodiode and LED are somewhat specific for that machine. But [tmbarbour] has included STL files in his exhaustively detailed write-up, so modifying them to fit another machine should be easy. The sensor hangs down just far enough to watch a reflector on one of the flats of the collet nut; we’d worry about the reflector surviving tool changes, but it’s just a piece of shiny tape that’s easily replaced. The sensor feeds into a DIO pin on a Nano, and a small OLED display shows a digital readout along with an analog gauge. The display update speed is decent — not too laggy. Impressive build overall, and we like the idea of using a piece of PLA filament as a rivet to hold the diodes into the sensor arm.
The CNC router in question is the popular Sienci, and the 3D-printed brackets for the photodiode and LED are somewhat specific for that machine. But [tmbarbour] has included STL files in his exhaustively detailed write-up, so modifying them to fit another machine should be easy. The sensor hangs down just far enough to watch a reflector on one of the flats of the collet nut; we’d worry about the reflector surviving tool changes, but it’s just a piece of shiny tape that’s easily replaced. The sensor feeds into a DIO pin on a Nano, and a small OLED display shows a digital readout along with an analog gauge. The display update speed is decent — not too laggy. Impressive build overall, and we like the idea of using a piece of PLA filament as a rivet to hold the diodes into the sensor arm.








