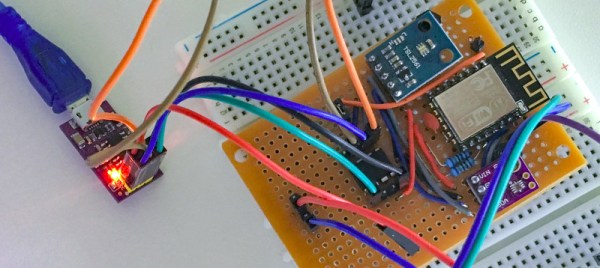
While the ESP8266 has made its way into virtually every situation where a low-cost WiFi solution is needed, it’s not known as being a low-power solution due to the amount of energy it takes to run WiFi. [Alex] took this design constraint as more of a challenge though, and with the help of an ATtiny microcontroller was able to develop a weather station using an ESP8266 that only needs new batteries every 2-4 years.
While the ESP8266 module consumes a bit of power, the ATtiny excels in low-power mode. To take advantage of this, [Alex] designed the weather station using the ATtiny to gather data every two minutes, store the data in a buffer, and upload all of it in bursts every hour using the ESP8266. This means that the power-hungry WiFi chip can stay off most of the time, drastically limiting the power demands of the station. [Alex] mostly details the setup of the ATtiny and the ESP8266 on his project page, so this could be applied anywhere that low power and network connectivity are required.
As for the weather reporting capabilities, the station is equipped to measure temperature, light, and humidity. Presumably more could be added but this might increase the power demands for the weather station as a whole. Still, changing batteries once a year instead of once every two years might be a worthwhile trade-off for anyone else attempting such an ambitious project. Other additions to the weather station that we’ve seen before might include a low-power display, too.