If you follow [Maker’s Muse] on YouTube, you know he’s as passionate about robot fights these days as he is about the tools he uses to make the robots. Luckily for us, he’s still got fame as a 3D printing YouTuber, as this has given him the platform to share his trade secrets for strong, robot-combat-worthy prints.
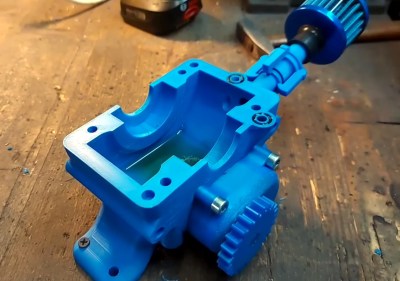
He fights robots in a ‘plastic ant-weight’ division, which restricts not only the weight of the robot but also the materials used. Not only must they be primarily plastic, but only certain plastics are allowed: PLA is in, but engineering filaments, Nylon, and TPU are out. Since necessity is the mother of invention, this has led to strong evolutionary pressure to figure out how to print the most impact-resilient PLA parts for armor and spinners.
He’s using the latest OrcaSlicer and shares the profile as a pay-what-you-want 3MF file. It’s all about solidity: a solid part with solidly fused walls and solidly linked layers. It makes sense: if you’re going to be hammering on or with these parts, you don’t want any internal voids that could either collapse or pull open.
The infill density is obviously 100%, and you’ll want a concentric pattern — this makes it look like you’re just printing walls, but it allows you to use another trick. To make sure those walls don’t all align, creating a potential weakness, OrcaSlicer’s “alternate extra wall” will put one extra wall every second layer. The extra wall causes the infill pattern to stagger and lock together.
Also helping lock it together, he’s playing with extrusion widths, with the suggested rule-of-thumb being the line width on the walls be one-half that of the internal fill — and as wide as possible. In his case, with a 0.4 mm nozzle, that means 0.4 mm wide walls and 0.8 mm for the infill. OrcaSlicer 2.3.2 also lets you play with specific flow ratios, allowing you to overextrude only the internals for strength, without overextruding on the walls and potentially ruining dimensional accuracy. He also irons all top surfaces, but admits that that’s mostly about aesthetics. The iron may make those layers a little bit stronger, though, so why not?
Would brick layers make these parts even stronger? That’s very likely; [Maker’s Muse] mentions them in the video but does not use them because they’re not implemented in-slicer, and he wants something accessible to all. On the other hand, this post-processing script seems accessible enough for our crowd.
This video/profile is exclusively about fully-solid parts. When you want strong parts that aren’t fully solid, it looks like the answer is walls.
, Continue reading “Slicer Settings For “Indestructible” Battle-Bot Worthy PLA Parts”