There are a bunch of ways to estimate the age of a radio amateur, by the letters in their callsign, by their preferred choice of homebrewing technology, or sometimes by their operating style. One that perhaps doesn’t immediately come to mind is to count how many solar cycles they remember, and since the current cycle 25 is my fourth I guess I’ve seen a few. Cycle 25 is so far shaping up to be quite an active one especially of late, which popular media are describing as bombarding us with flares from a “sunspot archipelago” and the more measured tones of spaceweather.com giving us warning of X-class flares heading in our direction, today!

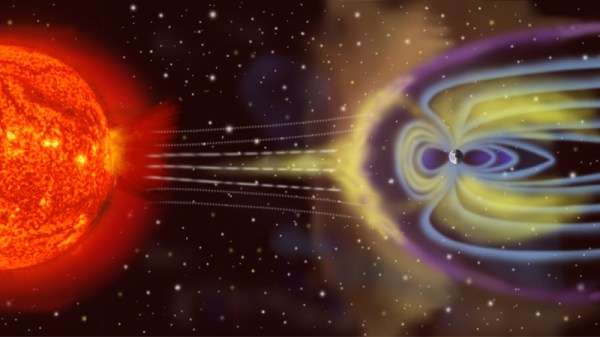
As the technology for solar observation has increased in sophistication and the Internet has allowed anyone to follow the events above us as they unfold, the awareness of solar phenomena has shifted away from the relatively small numbers of astronomers and radio amateurs who would once have been eagerly awaiting a solar cycle to a wider audience. Ever since a particularly severe event in March 1989 during cycle 22 caused disruptions including the blackout of a significant part of Canada it’s been a periodic topic of mild doom in slow news moments. But what lies behind the reports of solar activity? Perhaps it’s time to take a look.
The solar cycle refers to the 11-year period of solar activity from a maximum of observed sunspots through a minimum to a new maximum. The sunspots are the visible evidence of the solar magnetic field changing its polarity, and appear as darker areas where there is a greater strength of magnetic flux in the sun’s photosphere. We refer to solar cycles by number with solar cycle 1 occurring in 1755 because that year represents the earliest cycle which can be found in modern astronomical observation data, but previous cycles have been deduced over millennia through dendrochronology, sediment analysis, isotope observations, and other methods. Continue reading “The Sunspots Are Coming (Again)”