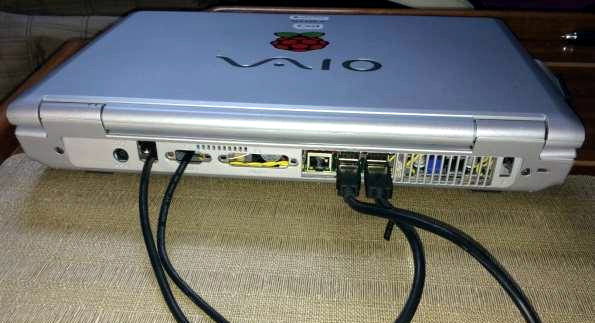
Early in November we took a look at a one of the best Raspberry Pi laptops we had ever seen, using the shell of a Sony VAIO. Laptops used to be hulking beasts, and that played into [Frank Adams’] hands as he got rid of the motherboard and had enough space to replace it with a Raspberry Pi and a few other support boards. This took advantage of the laptop’s screen, keyboard, LEDs, etc. But what’s a laptop without battery power? [Frank] hadn’t cracked that nut until now.

Adding battery power is trickier that it sounds, but [Frank] managed to get the Raspberry Pi to talk to the original Sony VAIO internal battery. His work on the project is shared, but this part of the story is best found starting on page 29 of his PDF project details.
Using the original battery is a good move since it’s designed to fit and has a charger ready to interface with the port on the laptop case. But these batteries have logic inside them, and there’s the rub. Communications use the 2-wire System Management Bus (SMBus) which is well documented. But the when trying to use the Pi’s I2C [Frank] couldn’t figure out to send a repeated start command.
He ended up writing his own C program that bit-bangs the communications he needed and now has the Pi speaking to the battery and listening to what it hears coming back. Reading through his description of this is fun since he includes his observations from a logic analyzer captures. He suspects an occasional bad read is due to Linux interrupting code execution. He watches for and catches these bad reads in software and can now reliably read all the battery vitals.
The hack leaves him with a system that functions in much the same way the original computer did: plug it in and it charges. He did add some hardware that lets him take a voltage reading from the battery using an ADC on the Teensy that was already present to control the keyboard and case LEDs. This adds a small constant draw on the battery, but for now he doesn’t leave the battery connected when the laptop is not in use.
If you’d like to read our original coverage of this laptop, here it is.

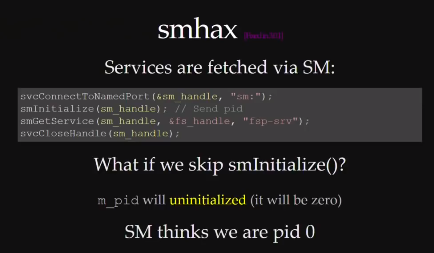


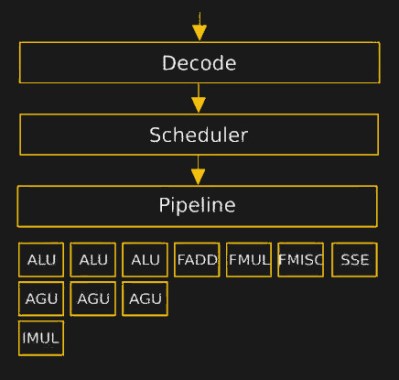 The hurdles to playing around in the microcode are daunting. It turns assembly language into something, but the instruction set that the inner CPU, ALU, et al use was completely unknown. [Philip] walked us through their first line of attack, which was essentially guessing in the dark. First they mapped out where each x86 assembly codes went in microcode ROM. Using this information, and the ability to update the microcode, they could load and execute arbitrary microcode. They still didn’t know anything about the microcode, but they knew how to run it.
The hurdles to playing around in the microcode are daunting. It turns assembly language into something, but the instruction set that the inner CPU, ALU, et al use was completely unknown. [Philip] walked us through their first line of attack, which was essentially guessing in the dark. First they mapped out where each x86 assembly codes went in microcode ROM. Using this information, and the ability to update the microcode, they could load and execute arbitrary microcode. They still didn’t know anything about the microcode, but they knew how to run it.