As ARRL president, [Rick Roderick, K5UR] spends a significant amount of time proselytising the hobby. He has a standard talk about amateur radio that involves tales gleaned from his many decades as a licence holder, and features QSL cards from rare DX contacts to show how radio amateurs talk all over the world.
He’s delivered this talk countless times, and is used to a good reception from audiences impressed with what can be done with radio. But when he delivered it to a group of young people, as Southgate ARC reports, he was surprised to see a lack of interest from his audience, to whom DX or contesting just don’t cut it when they have grown up with the pervasive Internet. Writing in the 2016 ARRL Annual Report, he said:
“Change generally doesn’t come easy to us. But when I looked out at that group of young faces and saw their disinterest in traditional ham pursuits, I realized that I had to change. We have to change. It won’t come easy, but it’s essential that we get to work on it now.”
If you were to profile a typical group of radio amateurs, it would not be difficult to see why [K5UR] found himself in this position. It might be an unflattering portrait for some amateurs, but it’s fair to say that amateur radio is a hobby pursued predominantly by older more well-off men with the means to spend thousands of dollars on commercial radios. It is also fair to say that this is hardly a prospect that would energize all but the most dedicated of youthful radio enthusiasts. This is not a new phenomenon, where this is being written it was definitely the case back in the days when they were issuing G7 callsigns, for instance.
Were Hackaday to find ourselves in the position of advising the ARRL on such matters, we’d probably suggest a return to the roots of amateur radio, a time in the early 20th century when it was the technology that mattered rather than the collecting of DXCC entities or grid squares, and an amateur had first to build their own equipment rather than simply order a shiny radio before they could make a contact. Give a room full of kids a kit-building session, have them make a little radio. And lobby for construction to be an integral part of the licensing process, it is very sad indeed that where this is being written at least, the lowest tier of amateur radio licence precludes home-made radio equipment. Given all that, why should it be a surprise that for kids, amateur radio just isn’t exciting?
We’ve shown you some fantastic amateur radio builds over the years. If you have a youngster with an interest in radio, show them a BitX transceiver, or the world of QRP.
Header image: enixii. [CC BY 2.0]. We hope these snoozing kids aren’t in the middle of a lecture on amateur radio.



















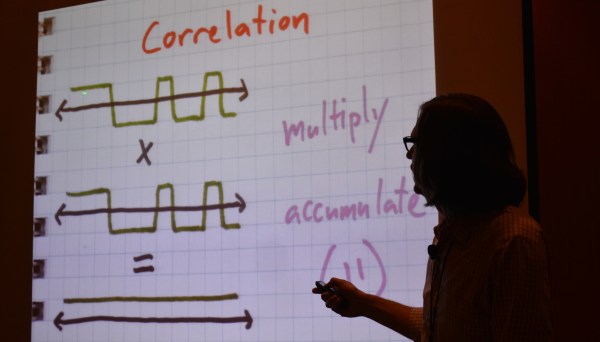


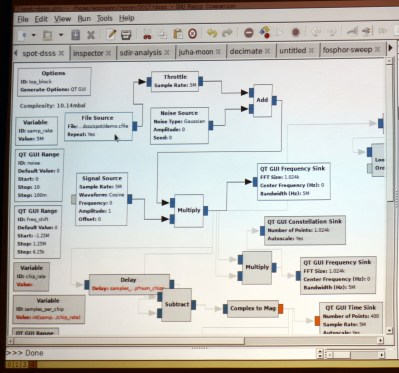 [Michael] mentioned simple math tricks, and he wasn’t kidding. It’s easy to assume that someone as experienced in RF as he would have a different definition of ‘simple’ than we would. But truly, he’s using multiplication and subtraction to do an awful lot.
[Michael] mentioned simple math tricks, and he wasn’t kidding. It’s easy to assume that someone as experienced in RF as he would have a different definition of ‘simple’ than we would. But truly, he’s using multiplication and subtraction to do an awful lot.