Every so often we run across something in the Hackaday tip line that sends us scurrying to Google, trying to source a component, part, or assembly. The ESP8266 WiFi module is the latest, made interesting because it pretty much doesn’t exist outside China.
Why is it cool? It’s a WiFi module with an SOC, making it somewhat similar to TI’s CC300 in conception (A.K.A. the thing that makes the Spark Core so appealing), in that a microcontroller on the module takes care of all the WiFi, TCP/IP stack, and the overhead found in an 802.11 network. It’s addressable over SPI and UART, making this an exceptionally easy choice for anyone wanting to build an Internet of Things thing; you can simply connect any microcontroller to this module and start pushing data up to the Internet. Oh, it’s also being sold for $5 in quantity one. Yes, for five dollars you can blink a LED from the Internet. That’s about half the price as the CC3000 itself, and a quarter of the price if you were to build a CC3000 breakout board.
There’s a catch, right, there’s always a catch. Yep. About two hours after this post is published it will be the number one English language Google result for “ESP8266.” As far as the English-speaking world is concerned, there is absolutely nothing to be found anywhere on the Internet on this module.
Seeed Studio recently sold a few of these modules for $7 and has some documentation, including a full datasheet and an AT command set. All the documentation is in Chinese. There’s also an “ESP8266 IoT SDK”, but from a quick glance at the code, this appears to be an SDK for the SOC on the module, not a simple way to connect the module to a microcontroller.
Anyone wanting to grab one of these modules can do so on Ali Express. Anyone wanting to do something with one of these modules will have a much more difficult time, most likely poking and prodding bits randomly with the help of Google translate. Should someone, or even a group of people, want to take up the task of creating a translation of the datasheet and possibly a library, we have a pretty collaborative project hosting site where you can do that. You may organize in the comments below; we’ll also be taking bets as to when a product using the ESP8266 will be found on Kickstarter. My guess is under a month.
EDIT: Here’s a translation of the datasheet and AT command set.
Edit two: [bafeigum] is writing a library go help him out.
Thanks [Liam] for the tip.




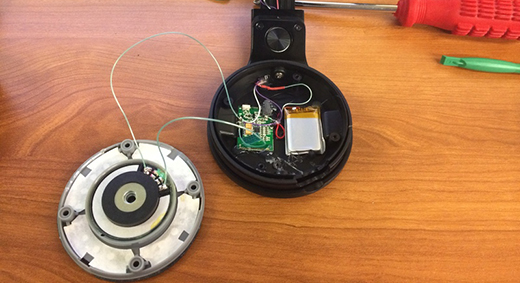
 With a simple $35 dongle that plugs right into your TV, it’s possible to enjoy your favorite TV shows, YouTube channels, and everything else Chromecast has to offer. Being a WiFi enabled device, it’s also possible to hijack a Chromecast, forcing your neighbors to watch
With a simple $35 dongle that plugs right into your TV, it’s possible to enjoy your favorite TV shows, YouTube channels, and everything else Chromecast has to offer. Being a WiFi enabled device, it’s also possible to hijack a Chromecast, forcing your neighbors to watch 








