Many of us regularly move from one computer to another for work, play, and hacking; every now and then finding yourself wishing you could copy something on one machine and paste on another without additional steps in between. [Ayan Pahwa] was well acquainted with this frustration, so he created AnywhereDoor, a cross-platform clipboard sharing utility that uses MQTT.
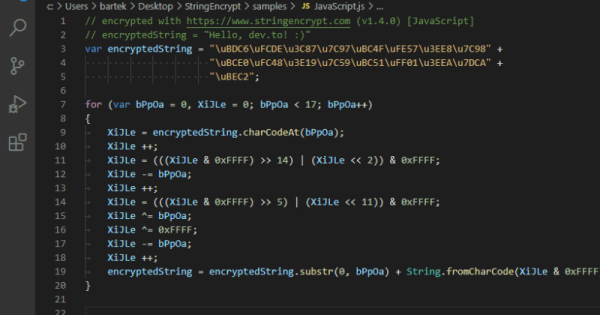
Some cloud-based solutions already exist to do this, but that means sending your private clipboard data to someone else’s server. Not keen on that idea, [Ayan]’s solution makes use of a MQTT broker that can run anywhere on the local network, and lightweight python clients to run on Mac, Windows and Linux. The client checks your clipboard at specified intervals, and publishes new data to a topic on the broker, to which all the clients are subscribed. The data is end-to-end encrypted using Fernet symmetrical key encryption, so the data won’t be readable to anyone else on the network. Currently, AnywhereDoor only supports copying text, but media is planned for a future version.
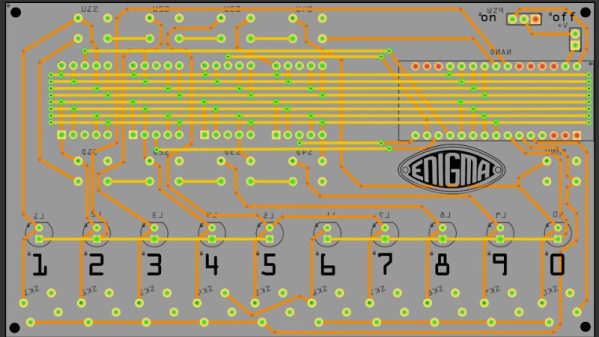
We like the relative simplicity of the utility, and see it being very handy for hackers bouncing between machines in the lab. Simple software utilities that solve a specific and real problem can are very useful, like a wiring documentation tool, or Kicad to isolation routing patchwork converter.