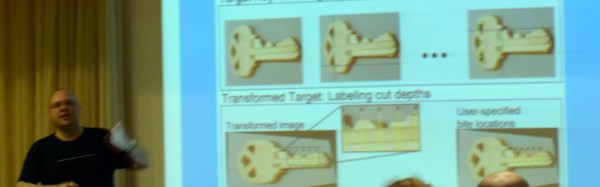
We’re at LayerOne this weekend and one of the talks we were excited about didn’t disappoint. [Jos Weyers] presented Showing Keys in Public — What Could Possibly Go Wrong? The premise is that pictures of keys, in most cases, are as good as the keys themselves. And that pictures of keys keep getting published.
[Jos] spoke a bit about new services that offer things like 3D scanning and storage of your key for printing when you get locked out, or apps that ask you to take a picture of your key and they’ll mail you a duplicate. Obviously this isn’t the best of ideas; you’re giving away your passwords. And finding a locksmith is easier than findind a 3D printer. But it’s the media gaffs with important keys that intrigues us.
We’ve already seen the proof of concept for taking covert images to perfectly duplicate a key. But these examples are not so covert. One example is a police officer carrying around handcuff keys on a belt clip. Pose for a picture and that key design is now available to all. But news stories about compromised keys are the biggest offenders.
 A master key for the NYC Subway was compromised and available for sale. The news coverage not only shows a picture at the top of the story of a man holding up the key straight on, but this image of it on a subway map which can be used to determine scale. This key, which is still published openly on the news story linked above, opens 468 doors to the subway system and these are more than just the ones that get you onto the platform for free. We were unable to determine if these locks have been changed, but the sheer number of them has us thinking that it’s unlikely.
A master key for the NYC Subway was compromised and available for sale. The news coverage not only shows a picture at the top of the story of a man holding up the key straight on, but this image of it on a subway map which can be used to determine scale. This key, which is still published openly on the news story linked above, opens 468 doors to the subway system and these are more than just the ones that get you onto the platform for free. We were unable to determine if these locks have been changed, but the sheer number of them has us thinking that it’s unlikely.
 Worse, was the availability of fire-department
Worse, was the availability of fire-department master keys which open lock boxes outside of every building. (Correction: these are fire department keys but not the actual lock-box keys) A locksmith used to cut the original keys went out of business and sold off all their stock. These keys were being sold for $150, which is bad enough. But the news coverage showed each key on a white background, straight on, with annotations of where each type of key will work.
Other examples include video news stories about credit card skimmers installed in gas pumps — that coverage showed the key used to open the pump housing. There was also an example of speed camera control cabinet keys being shown by a reporter.
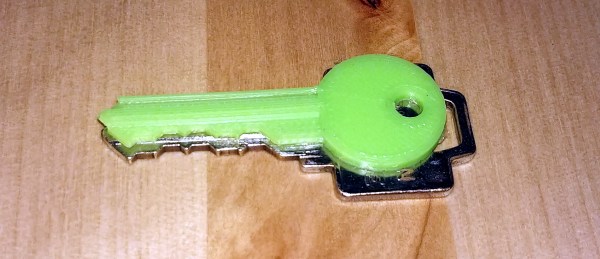
 [Jos’] example of doing the right thing is to use a “prop” key for news stories. Here he is posing with a key after the talk. Unfortunately this is my own house key, but I’m the one taking pictures and I have blurred the teeth for my own security. However, I was shocked during image editing at the quality of the outline in the image — taken at 6000×4000 with no intent to make something that would serve as a source for a copy. It still came out remarkably clear.
[Jos’] example of doing the right thing is to use a “prop” key for news stories. Here he is posing with a key after the talk. Unfortunately this is my own house key, but I’m the one taking pictures and I have blurred the teeth for my own security. However, I was shocked during image editing at the quality of the outline in the image — taken at 6000×4000 with no intent to make something that would serve as a source for a copy. It still came out remarkably clear.
Some locks are stronger than others, but they’re all meaningless if we’re giving away the keys.

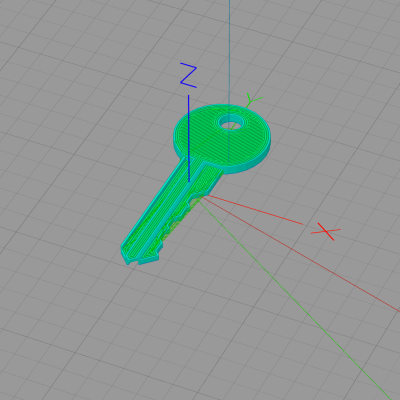 Rather than simply duplicating an existing key, [Dave] created a parametric key blank in OpenSCAD; he just enters his pin settings and the model generator creates the print file. He printed ABS on a glass plate with a schmeer of acetone on it, and .15mm layer heights. Another reason [Dave] chose Kwikset is that the one he had was super old and super loose — he theorizes that a newer, tighter lock might simply break the key.
Rather than simply duplicating an existing key, [Dave] created a parametric key blank in OpenSCAD; he just enters his pin settings and the model generator creates the print file. He printed ABS on a glass plate with a schmeer of acetone on it, and .15mm layer heights. Another reason [Dave] chose Kwikset is that the one he had was super old and super loose — he theorizes that a newer, tighter lock might simply break the key.


 A master key for the NYC Subway was compromised and available for sale.
A master key for the NYC Subway was compromised and available for sale.  Worse, was the availability of fire-department
Worse, was the availability of fire-department  [Jos’] example of doing the right thing is to use a “prop” key for news stories. Here he is posing with a key after the talk. Unfortunately this is my own house key, but I’m the one taking pictures and I have blurred the teeth for my own security. However, I was shocked during image editing at the quality of the outline in the image — taken at 6000×4000 with no intent to make something that would serve as a source for a copy. It still came out remarkably clear.
[Jos’] example of doing the right thing is to use a “prop” key for news stories. Here he is posing with a key after the talk. Unfortunately this is my own house key, but I’m the one taking pictures and I have blurred the teeth for my own security. However, I was shocked during image editing at the quality of the outline in the image — taken at 6000×4000 with no intent to make something that would serve as a source for a copy. It still came out remarkably clear.









