Off-the-shelf stock parts are the blocks from which we build mechanical projects. And while plenty of parts have dedicated uses, I enjoy reusing them in ways that challenge what they were originally meant for while respecting the constraints of their construction. Building off of my piece from last time, I’d like to add to your mechanical hacking palette with four more ways we can re-use some familiar off-the-shelf parts. Continue reading “The BSides: More Curious Uses Of Off-the-shelf Parts”
tricks7 Articles
These Capacitors Are A Cheap Gimmick
If you search through an electrical engineering textbook, you probably aren’t going to find the phrase “gimmick capacitor” but every old ham radio operator knows about them. They come in handy when you need a very small capacitor of unknown value. For example, if you are trying to balance the stray capacitance in a circuit, you might not know exactly what value you need, but you know it won’t be very much. That’s when you want a gimmick capacitor.
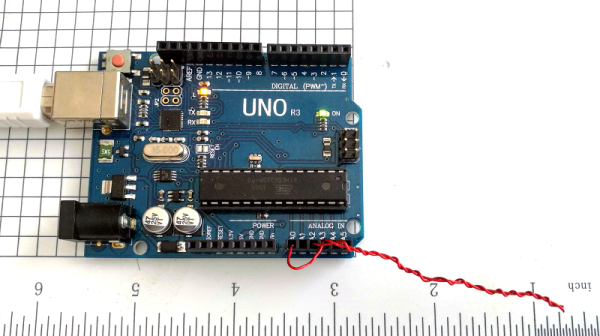
A gimmick capacitor is made by taking two strands of insulated wire and twisting them together; the length and the tightness of the twist determine the capacitance. Tightening or loosening the twist, or trimming some of the wire off, makes it tunable.
These are most commonly found in RF equipment or high-speed logic because of the small capacitance involved — usually about 1 to 2 pF per inch of twist or so. The thicker the insulation, the less capacitance you’ll get, so it is common to use magnet wire or something else with a thin insulating layer. You can take this one step further and decrease the spacing by stripping down one wire as long as it isn’t going to touch anything else.
Obviously, the insulation needs to be good enough for the voltage on them, an important consideration in tube circuits, for instance. But other than that, a gimmick capacitor is a straightforward tool to have in your box of design tricks. Can we take this further? Continue reading “These Capacitors Are A Cheap Gimmick”
RoGeorge Attacks A Pulse Meter
The “Crivit Sports” is an inexpensive chest-strap monitor that displays your current pulse rate on a dedicated wristwatch. This would be much more useful, and presumably more expensive, if it had a logging option, or any way to export your pulse data to a more capable device. So [RoGeorge] got to work. Each post of the (so-far) three-part series is worth a read, not the least because of the cool techniques used.
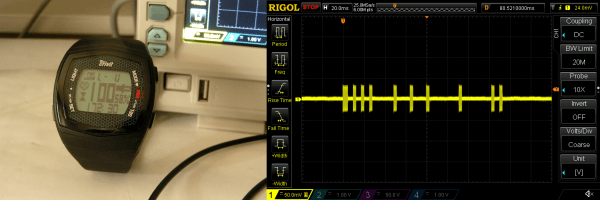
 In part one, [RoGeorge] starts out by intercepting the signals. His RF sniffer? An oscilloscope probe shorted out in a loop around the heart monitor. Being able to read the signals, it was time to decode them. Doing pushups and decoding on-off keyed RF signals sounds like the ideal hacker training regimen, but instead [RoGeorge] used a signal generator, clipped to the chest monitor, to generate nice steady “heartbeats” and then read the codes off the scope without breaking a sweat.
In part one, [RoGeorge] starts out by intercepting the signals. His RF sniffer? An oscilloscope probe shorted out in a loop around the heart monitor. Being able to read the signals, it was time to decode them. Doing pushups and decoding on-off keyed RF signals sounds like the ideal hacker training regimen, but instead [RoGeorge] used a signal generator, clipped to the chest monitor, to generate nice steady “heartbeats” and then read the codes off the scope without breaking a sweat.
With the encoding in hand, and some help from the Internet, he tested out his hypothesis in part two. Using an Arduino to generate the pulses logged in part one, he pulsed a coil and managed to get the heart rates displayed on the watch.
Which brings us to part three. What if there were other secrets to be discovered? Brute-forcing every possible RF signal and looking at the watch to see the result would be useful, but doing so for 8,192 possible codes would drive anyone insane. So [RoGeorge] taught himself OpenCV in Python and pointed a webcam at the watch. He wrote a routine that detected the heart icon blinking, a sign that the watch received a valid code, and then transmitted all possible codes to see which ones were valid. Besides discovering a few redundant codes, he didn’t learn much new from this exercise, but it’s a great technique.
We’re not sure what’s left to do on the Crivit. [RoGeorge] has already figured out the heart-rate data protocol, and could easily make his own logger. We are sure that we liked his thorough and automated approach to testing it all, from signal-generator-as-heartbeat to OpenCV as feedback in a brute-force routine. We can’t wait to see what’s up next.
Blob Grid Array Technique Mounts Board-To-Board
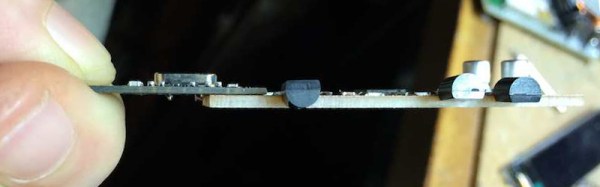
[Howard Matthews] mills his own PCBs, and man, does he hate drilling through-holes. Manually changing the bits between engraving and drilling after isolation routing? What is this? The stone age? [Howard] decided to rethink his DIY PCB manufacturing process, and came to one essential conclusion: Only a fraction of these drills are actually necessary.
Continue reading “Blob Grid Array Technique Mounts Board-To-Board”
Drones, Clever Hacks, And CG Come Together For Star Wars Fan Film
We weren’t certain if this Star Wars fan film was out kind of thing until we saw the making of video afterwards. They wanted to film a traditional scene in a new way. The idea was to take some really good quadcopter pilots, give them some custom quadcopters, have them re-enact a battle in a scenic location, and then use some movie magic to bring it all together.
The quadcopters themselves are some of those high performance racing quadcopters with 4K video cameras attached. The kind of thing that has the power to weight ratio of a rocket ship. Despite what the video implies, they are unfortunately not TIE Fighter shaped. After a day of flying and a few long hikes to retrieve the expensive devices after inevitable crashes (which, fortunately, provided some nice footage), the next step was compositing.
However, how to trick the viewer into believing they were in a X-Wing quadcopter? A cheap way to do it would be to spend endless hours motion tracking and rendering a cockpit in place. It won’t look quite real. The solution they came up with is kind of dumb and kind-of brilliant. Mount a 3D printed cockpit on a 2×4 with a GoPro. Play the flight footage on a smartphone while holding the contraption. Try to move the cockpit in the same direction as the flight. We’re not certain if it was a requirement to also make whooshing and pew pew laser noises while doing so, but it couldn’t hurt.
In the end it all came together to make a goofy, yet convincingly good fan film. Nice work! Videos after the break.
Continue reading “Drones, Clever Hacks, And CG Come Together For Star Wars Fan Film”
What’s Happening At LIFE.hackaday Lateley
 If you haven’t been over to LIFE.hackaday lately, maybe you should check it out.
If you haven’t been over to LIFE.hackaday lately, maybe you should check it out.
You could be learning how to be a hero with a wine cork, or how to easily break string without scissors(or your teeth). Need new ways to mount your tablet? We’ve got you covered. However, the story that is probably most important right now is how to keep your ice cream from getting that freezer burnt section on the top.
Five Plugins And Tips To Secure Your WordPress Blog
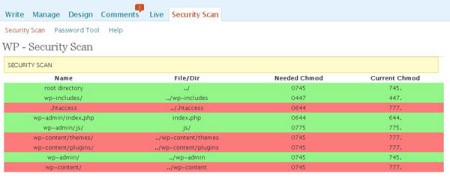
How do you protect your own blog from getting hacked? There’s never a foolproof answer, but with some added tools and caution, you can make your website a little safer from getting into harm’s way. Cats Who Code has five plug-ins and tips you can use to protect your WordPress install. Some of the tips are common sense advice that can apply to anything related to technology – such as making backups often and using strong passwords. Others include suggested plugins that can help you verify whether your WordPress install has any security holes, or small tricks to hide the version of WordPress you’re using. Do you have any useful plugins or tricks to share to keep your blog safe from hackers?
[via Digg]