How worn are your nozzles? It’s a legitimate question, so [Stefan] set out to find out just how bad 3D-printer nozzle wear can get. The answer, as always, is “It depends,” but exploring the issue turns out to be an interesting trip.
Reasoning that the best place to start is knowing what nozzle wear looks like, [Stefan] began by printing a series of Benchies with brand-new brass nozzles of increasing diameter, to simulate wear. He found that stringing artifacts, interlayer holes, and softening of overhanging edges and details all worsened with increasing nozzle size. Armed with this information, [Stefan] began a torture test of some cheap nozzles with both carbon-fiber filament and a glow-in-the-dark filament, both of which have been reported as nozzle eaters. [Stefan] found that to be the case for at least the carbon-fiber filament, which wore the nozzle to a nub after extruding only 360 grams of material.
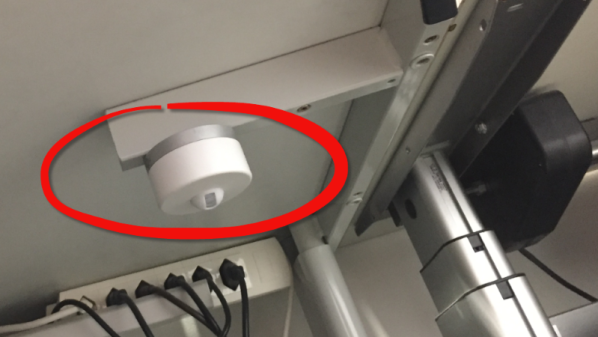
Finally, [Stefan] did some destructive testing by cutting used nozzles in half on the mill and looking at them in cross-section. The wear on the nozzle used for carbon-fiber is dramatic, as is the difference between brand-new cheap nozzles and the high-quality parts. Check out the video below and please sound off in the comments if you know how that peculiar spiral profile was machined into the cheap nozzles.
Hats off to [Stefan] for taking the time to explore nozzle wear and sharing his results. He certainly has an eye for analysis; we’ve covered his technique for breaking down 3D-printing costs in [Donald Papp]’s “Life on Contract” series.