In the race toward a future free from fossil fuels, hydrogen is rapidly gaining ground. On paper, hydrogen sounds fantastic — it’s clean-burning with zero emissions, the refuel time is much faster than electric, and hydrogen-fueled vehicles can go longer distances between refuels than their outlet-dependent brethren.
The reality is that hydrogen vehicles usually need fuel cells to convert hydrogen and oxygen into electricity. They also need pressurized tanks to store the gases and pumps for refueling, all of which adds weight, takes up space, and increases the explosive potential of the system.
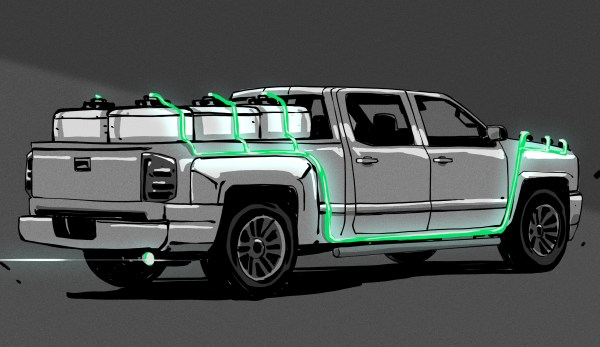
Kurt Koehler has a better idea: make the hydrogen on demand, in the vehicle, using a solid catalyst and a simple chemical reaction. Koehler is the founder of Indiana-based startup AlGalCo — Aluminium Gallium Company. After fourteen years of R&D and five iterations of his system, the idea is really starting to float. Beginning this summer, these pucks are going to power a few trucks in a town just outside of Indianapolis.