Tilt Five is an Augmented Reality (AR) system developed by Jeri Ellsworth and a group of other engineers that is aimed at tabletop gaming which is now up on Kickstarter. Though it appears to be a quite capable (and affordable at $299) system based on the Kickstarter campaign, the most remarkable thing about it is probably that it has its roots at Valve. Yes, the ones behind the Half Life games and the Steam games store.
Much of the history of the project has been covered by sites, such as this Verge article from 2013. Back then [Jeri Ellsworth] and [Rick Johnson] were working on project CastAR, which back then looked like a contraption glued onto the top of a pair of shades. When Valve chose to go with Virtual Reality instead of AR, project CastAR began its life outside of Valve, with Valve’s [Gabe] giving [Jeri] and [Rick] his blessing to do whatever they wanted with the project.

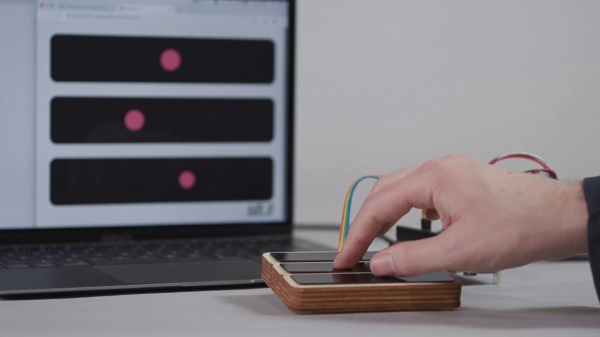
Six years later Tilt Five is the result of the work put in over those years. Looking more like a pair of protective glasses along with a wand controller that has an uncanny resemblance to a gas lighter for candles and BBQs, it promises a virtual world like one has never seen before. Courtesy of integrated HD projectors that are aimed at the retroreflective surface of the game board.
A big limitation of the system is also its primary marketing feature: by marketing it as for tabletop gaming, the fact that the system requires this game board as the projection surface means that the virtual world cannot exist outside the board, but for a tabetop game (like Dungeons and Dragons), that should hardly be an issue. As for the games themselves, they would run on an external system, with the signal piped into the AR system. Game support for the Tilt Five is still fairly limited, but more titles have been announced.
(Thanks, RandyKC)