Remember DarkTower? No? Well, it’s a really cool combination board game, RPG, and computer game from 1981. Orson Welles pimped it on TV and explained it thusly: “collect three keys, lay siege to the tower, and defeat the enemy within”. The Tower itself was a battery-powered computer on lazy Susan that showed numbers on a couple of 7-segment displays, pictures via three carousels, and had a 12-button keypad. Thanks to a lawsuit, few copies remain, and even fewer of them are in working condition.
 Working copies of DarkTower go for hundreds online, but who can afford such an extravagance when these 40+ year old towers are prone to battery leakage and loose connections? Certainly not [Mighty Studios], who was hoping to give the gift of DarkTower to a friend and decided to build a mini reproduction instead. Fortunately for us, the project is completely open source. You can check out the build video below, which has plenty of links, including one that goes to the code.
Working copies of DarkTower go for hundreds online, but who can afford such an extravagance when these 40+ year old towers are prone to battery leakage and loose connections? Certainly not [Mighty Studios], who was hoping to give the gift of DarkTower to a friend and decided to build a mini reproduction instead. Fortunately for us, the project is completely open source. You can check out the build video below, which has plenty of links, including one that goes to the code.
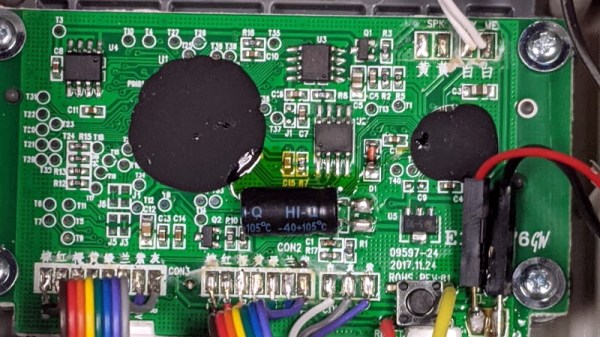
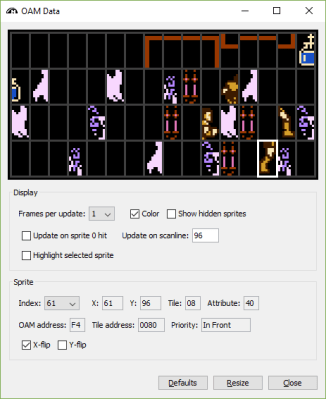
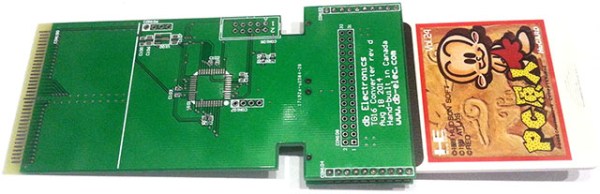
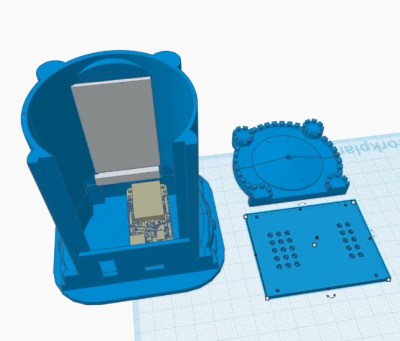
In this day and age, it doesn’t take much to reproduce the internals of the Tower. [Mighty Studios] pulled it off with a Feather S2, a 320 x 420 TFT LCD screen, a speaker, and a couple of momentary buttons. The screen can show all the pictures, (which were only displayed one at a time in the original game anyway), any necessary numbers, and all the requisite menu options.
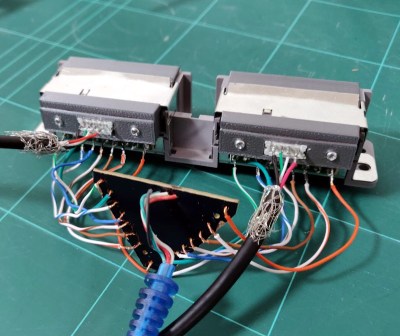
[Mighty Studios] got mighty lucky when it came to the case, as [Stinkevil] had already created a dice tower version and put it on Thingiverse. After a bit of tweaking and some hole-punching, [Mighty Studios] had a mini tower scaled to the Feather S2 with just enough room to stuff in all the components and wires. Between a PDF of the original rule book and someone’s Java version of the game, [Mighty Studios] had plenty to use as a guide for programming in the rule set before mailing it off to their friend. We have to admit, we’re pretty jealous.
Don’t want to amass an army and conquer evil forces? There are all types of board games you could emulate with a microcontroller.
Continue reading “Mini DarkTower Clone Restores Your Childhood”