The Quadrivium EnsembleBot project is a mashup between old school musical instruments and the modern MIDI controlled world. Built by a small team over several years, these hand crafted instruments look and sound really nice.
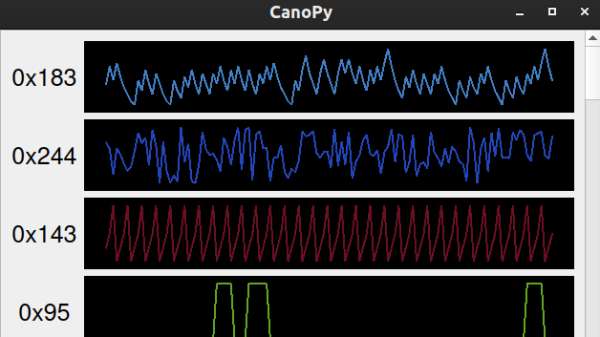
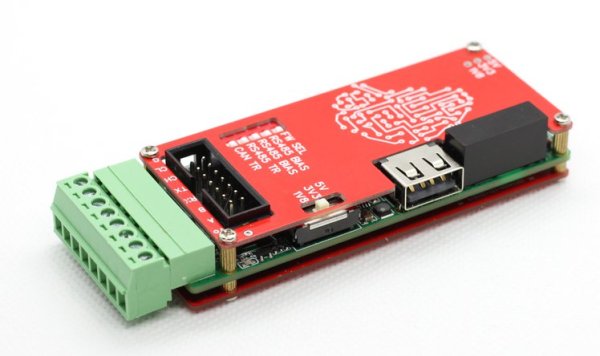
The electronics side of things is taken care of with a pile of Arduinos and off-the-shelf modules, but that doesn’t mean the design isn’t well thought through, if a little more complicated than it could be in places. Control is taken care of with a PC sending commands over the USB to an Arduino 2560. This first Arduino is referred to as the Master Controller and has the immediate job of driving the percussive instruments as well as other instruments that are struck with simple solenoids. All these inductive loads are switched via opto-isolators to keep any noise generated by switching away from the microcontroller. A chain of four sixteen-channel GPIO expander modules are hung off the I2C bus to give even more opto-isolated outputs, as even the Arduino 2560 doesn’t quite have enough GPIO pins available. The are a number of instruments that have more complex control requirements, and these are connected to dedicated slave Arduinos via an SPI-to-CAN module. These are in various states of development, which we’ll be keeping our beady eyes on.
One of the more complex instruments is the PipeDream61 which is their second attempt to build a robotic pipe organ. This is powered by a Teensy, as they considered the Arduino to be a little too tight on resources. This organ has a temperature controller using an ATTiny85, in order to further relieve the main controller of such a burden and simplify the development a little.
Another interesting instrument is Robro, which is a robotic resophonic guitar which as they say is still work in progress despite how long they have been trying to get it to work. There’s clearly a fair bit of control complexity here, which is why it is taking so much fiddling (heh!) to get it work.
This project is by no means unique, lately we’ve covered controlling a church organ with MIDI, as well as a neat Arduino Orchestra, but the EnsembleBot is just so much more.
Continue reading “The Quadrivium EnsembleBot Is A Labour Of Love”