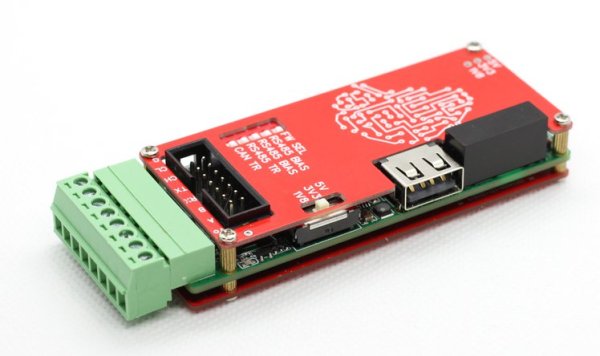
We’re used to interfaces such as I2C and one-wire as easy ways to hook up sensors and other peripherals to microcontrollers. While they’re fine within the confines of a small project, they do have a few limitations. [Vinnie] ran straight into those limitations while using a Raspberry Pi with agricultural sensors. The interfaces needed to work over long cable runs, and to be protected from ESD due to lightning strikes. The solution? A custom Pi interface board packing differential drivers and protection circuits aplenty.
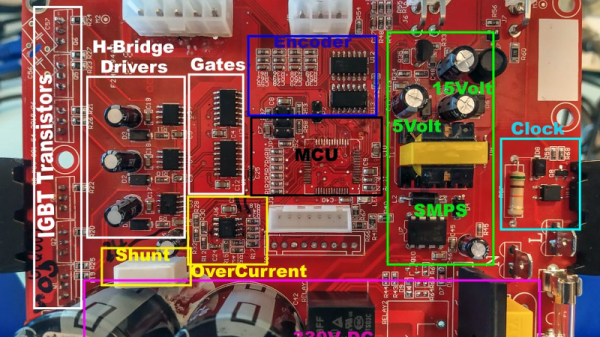
The I2C connection is isolated using an ISO1541 bus isolator from TI, feeding a PCA9615DP differential I2C bus driver from NXP. 1-wire is handled by a Dallas DS2482S 1-wire bus master and an ESD protection diode network. Even the 5-volt power supply is delivered through an isolated module.
Whether or not you need this Raspberry Pi board, this is still an interesting project for anyone working with these interfaces. If you’re interested, we’ve looked at differential I2C in the past.