Restoring pinball machines is an excellent hobby, and can even be more than that as we see businesses like bars and museums focusing on them as a main attraction. There’s all kinds of intrigue to be found, from esoteric mechanical systems to classic electronics and unique artwork. For those building new pinball machines, though, one way to bypass a lot of the hassle of finding antiquated parts is to build a digital machine with an analog feel, like this machine which repurposes a computer mouse in an interesting way.
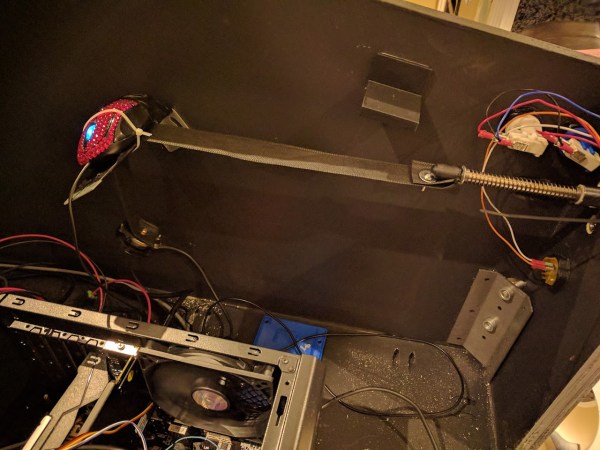
One of the important design considerations with a more modern system like this is to preserve the mechanical components that the player interacts with, in this case the plunger. This pinball machine is really just a large screen driven by a computer, but the plunger is a spring-loaded one from an old analog machine. Attached to the end of the plunger inside the cabinet is a cloth strap which passes underneath an old optical mouse. When the plunger is pulled and released, the mouse registers the position of the plunger and sends that information to the computer controlling the pinball display.
We really appreciate a KISS-style design like this in general. Mice are a proven, reliable technology and the metal components of the plunger are unlikely to ever wear out, which means that at least this part of the new pinball machine is unlikely to need much maintenance over the lifespan of the cabinet itself. For other ways of preserving the original feel of old machines, take a look at this build which incorporates all kinds of tricks within a MAME cabinet.



 This fermenter’s controller drives a heating element, which adheres to a pre-programmed fermentation cycle. It also has a fan for airflow and keeping the heat uniform.
This fermenter’s controller drives a heating element, which adheres to a pre-programmed fermentation cycle. It also has a fan for airflow and keeping the heat uniform.