When asked why he robbed banks, career criminal Willie Sutton is reported to have said, “Because that’s where the money is.” It turns out that a reporter made up the quote, but it’s a truism that offers by extension insight into why ATMs and point-of-sale terminals are such a fat target for criminals today. There’s something far more valuable to be taken from ATMs than cash, though — data, in the form of credit and debit card numbers. And taking a look at some of the hardware used by criminals to get this information reveals some pretty sophisticated engineering. We’d heard of ATM “skimmers” before, but never the related “shimmers” that are now popping up, at least according to this interesting article on Krebs.
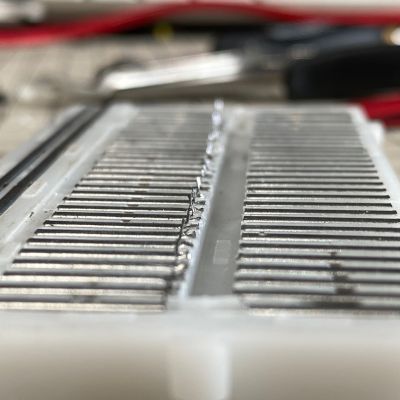
 While skimmers target the magnetic stripe on the back of a card, simmers are aimed at reading the data from card chips instead. Shimmers are usually built on flex PCBs and are inserted into the card slot, where traces on the device make contact with the chip reader contacts. The article describes a sophisticated version of shimmer that steals power from the ATM itself, rather than requiring a separate battery. The shimmer sits inside the card slot, completely invisible to external inspection (sorry, Tom), and performs what amounts to man-in-the-middle attacks. Card numbers are either stored on the flash and read after the device is retrieved, or are read over a Bluetooth connection; PINs are stolen with the traditional hidden camera method. While we certainly don’t condone criminal behavior, sometimes you just can’t help but admire the ingenuity thieves apply to their craft.
While skimmers target the magnetic stripe on the back of a card, simmers are aimed at reading the data from card chips instead. Shimmers are usually built on flex PCBs and are inserted into the card slot, where traces on the device make contact with the chip reader contacts. The article describes a sophisticated version of shimmer that steals power from the ATM itself, rather than requiring a separate battery. The shimmer sits inside the card slot, completely invisible to external inspection (sorry, Tom), and performs what amounts to man-in-the-middle attacks. Card numbers are either stored on the flash and read after the device is retrieved, or are read over a Bluetooth connection; PINs are stolen with the traditional hidden camera method. While we certainly don’t condone criminal behavior, sometimes you just can’t help but admire the ingenuity thieves apply to their craft.
In a bit of foreshadowing into how weird 2020 was going to be, back in January of that year we mentioned reports of swarms of mysterious UAVs moving in formation at night across the midwest United States. We never heard much else about this — attention shifted to other matters shortly thereafter — but now there are reports out of Arizona of a “super-drone” that can outrun law enforcement helicopters. The incidents allegedly occurred early this year, when a Border Patrol helicopter pilot reported almost colliding with a large unmanned aerial system (UAS) over Tucson, and then engaged them in a 70-mile chase at speeds over 100 knots. The chase was joined by a Tucson police helicopter, with the UAS reaching altitudes of 14,000 feet at one point. The pilots didn’t manage to get a good look at it, describing it only as having a single green light on its underside. The range on the drone was notable; the helicopter pilots hoped to exhaust its batteries and force it to land or return to base, but they themselves ran out of fuel long before the drone quit. We have to admit that we find it a little fishy that there’s apparently no photographic evidence to back this up, especially since law enforcement helicopters are fairly bristling with sensors, camera, and spotlights.
When is a backup not a backup? Apparently, when it’s an iCloud backup. At least that’s the experience of one iCloud user, who uses a long Twitter thread to vent about the loss of many years of drawings, sketches, and assorted files. The user, Erin Sparling, admits their situation is an edge case — he had been using an iPad to make sketches for years, backing everything up to an iCloud account. When he erased the iPad to loan it to a family member for use during the pandemic, he thought he’s be able to restore the drawings from his backups, but alas, more than six months had passed before he purchased a new iPad. Apparently iCloud just up and deletes everythign if you haven’t used the account in six months — ouch! We imagine that important little detail was somehere in the EULA fine print, but while that’s not going to help Erin, it may help you.
And less the Apple pitchfork crowd think that this is something only Cupertino could think up, know that some Western Digital external hard drive users are crying into their beer too, after a mass wiping of an unknown number of drives. The problem impacts users of the WD My Book Live storage devices, which as basically network attached storage (NAS) devices with a cloud-based interface. The data on these external drives is stored locally, but the cloud interface lets you configure the device and access the data from anywhere. You and apparently some random “threat actors”, as WD is calling them, who seem to have gotten into some devices and performed a factory reset. While we feel for the affected users, it is worth noting that WD dropped support for these devices in 2015; six years without patching makes a mighty stable codebase for attackers to work on. WD is recommending that users disconnect these devices from the internet ASAP, and while that seems like solid advice, we can think of like half a dozen other things that need to get done to secure the files that have accumulated on these things.
And finally, because we feel like we need a little palate cleanser after all that, we present this 3D-printed goat helmet for your approval. For whatever reason, the wee goat pictured was born with a hole in its skull, and some helpful humans decided to help the critter out with TPU headgear. Yes, the first picture looks like the helmet was poorly Photoshopped onto the goat, but scroll through the pics and you’ll see it’s really there. The goat looks resplendent in its new chapeau, and seems to be getting along fine in life so far. Here’s hoping that the hole in its skull fills in, but if it doesn’t, at least they can quickly print a new one as it grows.