Having a computer that locks its screen after a few minutes of inactivity is always a good idea from a security standpoint, especially in offices where there is a lot of foot traffic. Even the five- or ten-minute activity timers that are set on most workstations aren’t really perfect solutions. While ideally in these situations we’d all be locking our screens manually when we get up, that doesn’t always happen. The only way to guarantee that this problem is solved is to use something like this automatic workstation locker.
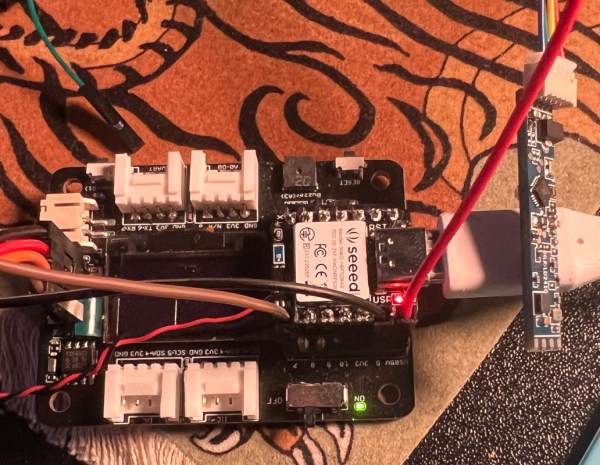
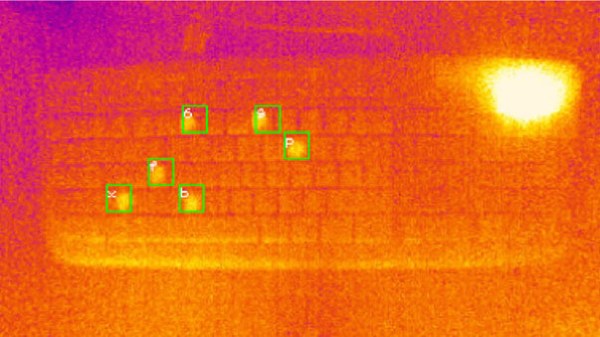
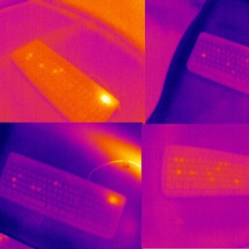
The project is based around the LD2410 presence sensor — a small 24 GHz radar module featuring onboard signal processing which simplifies the detection of objects and motion. [Enzo] paired one of these modules with a Seeed Studio XIAO nRF52840 development board to listen to the radar module and send the screen lock keyboard shortcut to the computer when it detects that the user has walked away from the machine. The only thing that [Enzo] wants to add is a blinking LED to let the user know when the device is about to timeout so that it doesn’t accidentally lock the machine when not needed.
One of the parts of this build that is a little bit glossed over is the fact that plenty of microcontroller platforms can send keystrokes to a computer even if they’re not themselves a USB keyboard. Even the Arduino Uno can do this, so by now this feature is fairly platform-agnostic. Still, you can use this to your advantage if you have the opposite problem from [Enzo] and need your computer to stay logged in no matter what.