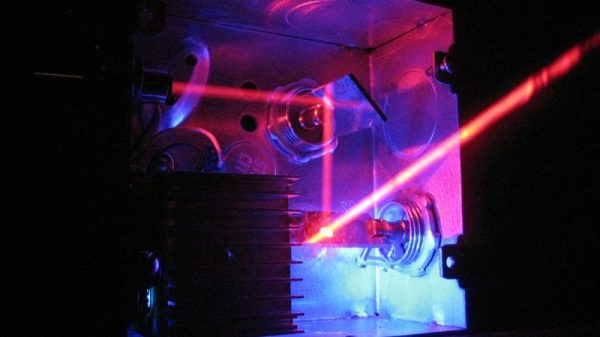
We’re suckers for any project that’s nicely packaged, but an added bonus is when most of the components can be sourced cheaply and locally. Such is the case for this little laser light show, housed in electrical boxes from the local home center and built with stuff you probably have in your junk bin.
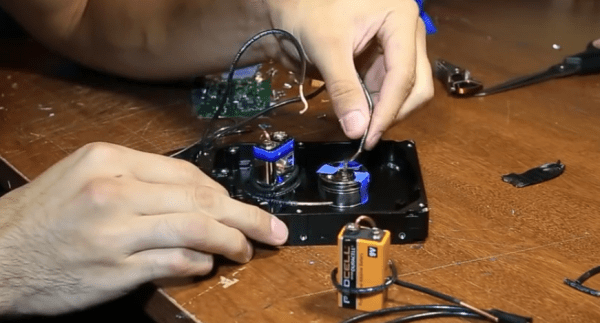
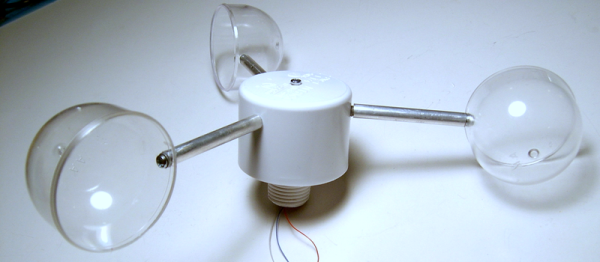
When we first came across [replayreb]’s write-up and saw that he used hard drives in its construction, we assumed he used head galvanometers to drive the mirrors. As it turns out, he used that approach in an earlier project, but this time around, the hard drive only donated its platters for use as low mass, first surface mirrors. And rather than driving the mirrors with galvos, he chose plain old brushed DC motors. These have the significant advantage of being cheap and a perfect fit for 3/4″ EMT set-screw connectors, designed to connect thin-wall conduit, also known as electromechanical tubing, to electrical boxes and panels. The motors are mounted to the back and side of the box so their axes are 90° from each other, and the mirrors are constrained by small cable ties and set at 45°. The motors are driven directly by the left and right channels of a small audio amp, wiggling enough to create a decent light show from the laser module.
We especially like the fact that these boxes are cheap enough that you can build three with different color lasers. In that case, an obvious next step would be bandpass filters to split the signal into bass, midrange, and treble for that retro-modern light organ effect. Or maybe figuring out what audio signals you’d need to make this box into a laser sky display would be a good idea too.
Continue reading “Little Laser Light Show Is Cleverly Packaged, Cheap To Build”