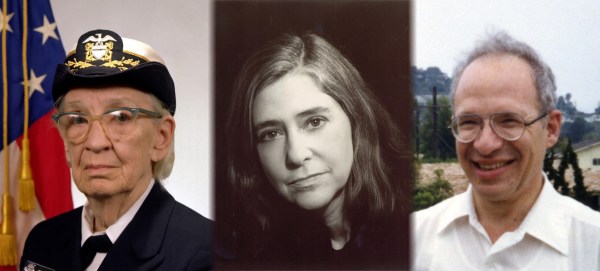
Somewhat hidden among athletes, actors, and musicians, three giants of technology have been aptly named as 2016 Presidential Medal of Freedom recipients. Grace Hopper, Margaret Hamilton, and Richard Garwin all made significant contributions to the technology that envelops our lives and embody the quest for knowledge and life-long self learning that we’d like to see in everyone.

Rear Admiral Grace Hopper’s legacy lies with the origins of computer science. She wrote the first compiler. In a time when computers were seen more as calculating machines than easily adaptable frameworks she looked to the future and made it happen. She continued to make huge contributions with lasting effect in developing COBOL, unit testing methods for programmers, and in education. We have long loved her explanation of a nanosecond (and why software engineers shouldn’t waste cycles) and was one of the first to program on the Harvard Mark I which can still be seen in the lobby of the school’s engineering building.
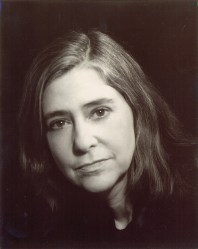 As Director of Apollo Flight Computer Programming, Margaret Hamilton is the driving force behind the software of Apollo. When the program started, she was Director of Software Engineering at MIT Instrumentation Laboratory. Originally there wasn’t a plan or budget for software in the space program. Hamilton built the program and led the team who wrote the software and turned it into punch cards to be fed into the computer. We enjoyed reading about some of her adventures during the Apollo project, her drive to develop pristine code is palpable. Over the past year we’ve marveled at the rope memory of the Apollo Guidance Computer and delighted when a hardcopy of AGC software showed up at a party. Her legacy at having written the code for the first portable computer — one that happened to land on the moon and return home safely — is incredible.
As Director of Apollo Flight Computer Programming, Margaret Hamilton is the driving force behind the software of Apollo. When the program started, she was Director of Software Engineering at MIT Instrumentation Laboratory. Originally there wasn’t a plan or budget for software in the space program. Hamilton built the program and led the team who wrote the software and turned it into punch cards to be fed into the computer. We enjoyed reading about some of her adventures during the Apollo project, her drive to develop pristine code is palpable. Over the past year we’ve marveled at the rope memory of the Apollo Guidance Computer and delighted when a hardcopy of AGC software showed up at a party. Her legacy at having written the code for the first portable computer — one that happened to land on the moon and return home safely — is incredible.
 Physicist Richard Garwin’s name is most associated with the first hydrogen bomb design. But another part of his work is more likely to have directly touched your life: his research into spin-echo magnetic resonance helped lead to the development of Magnetic Resonance Imaging. MRIs have of course become a fundamental tool in medicine. Garwin studied under Fermi during his doctoral work — you may remember Fermi from our look at the Fermiac analog computer last year.
Physicist Richard Garwin’s name is most associated with the first hydrogen bomb design. But another part of his work is more likely to have directly touched your life: his research into spin-echo magnetic resonance helped lead to the development of Magnetic Resonance Imaging. MRIs have of course become a fundamental tool in medicine. Garwin studied under Fermi during his doctoral work — you may remember Fermi from our look at the Fermiac analog computer last year.
Congratulations to these three recipients, their recognition is incredibly well deserved. We’d love to hear about some of your own technology heroes. Let us know on the tips line so that we may help celebrate their accomplishment and inspire the next generation of giants.
Image Credits:
- Photo of Grace Hopper By James S. Davis — Public Domain
- Photo of Margaret Hamilton By Daphne Weld Nichols — CC-BY-SA 3.0
- Photo of Richard Garwin by A.T. Service — CC-BY-SA 3.0



![A GPIB/IEEE488 plug. Alkamid [CC BY-SA 3.], via Wikimedia Commons](https://hackaday.com/wp-content/uploads/2016/10/a_gpib_plug.jpg?w=400)