Join us on Wednesday, February 26 at noon Pacific for the Hacking USB Hack Chat with Kate Temkin!
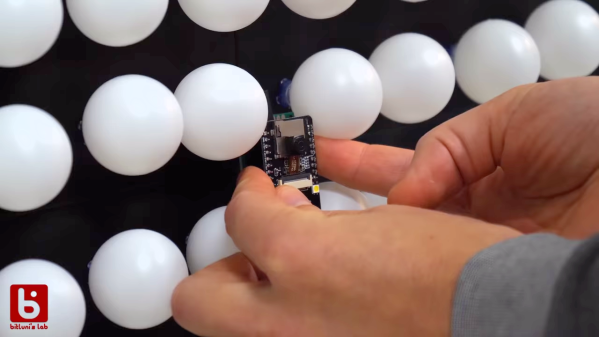
For all its aggravating idiosyncrasies, the Universal Serial Bus has been a game-changer in peripheral connections for nearly a quarter of a century now. What was once simply a means to connect a mouse and a keyboard to a computer has been extended and enhanced into something so much more than its original designers intended. The flexibility that led to these innovative uses for USB also led to its ubiquity, with some form of the connector sprouting from nearly every imaginable device.
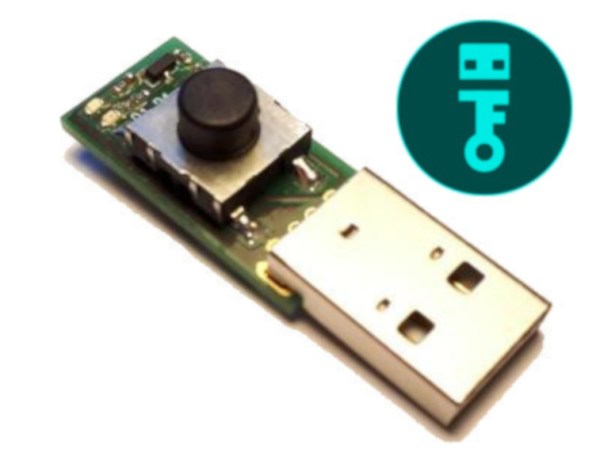
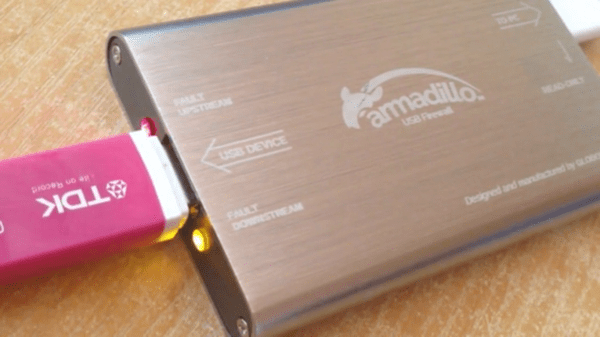
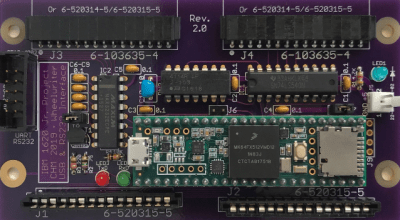
Kate Temkin is well-versed in the intricacies of the Universal Serial Bus. As a software lead for Great Scott Gadgets, Kate has developed software and firmware for GSG’s products, like GreatFET and HackRF. Kate also contributes to and maintains a number of open-source projects, including the FaceDancer project. And when she’s not busy with all of this, she can be found sharing her deep knowledge with USB security training courses, where she shows how USB is vulnerable to attack, and what to do to prevent it.
Join us for the Hacking USB Hack Chat this week, where Kate will discuss anything and everything about USB. Come learn about what the future holds for the USB standard, and what you can do to keep your USB project on track.
 Our Hack Chats are live community events in the Hackaday.io Hack Chat group messaging. This week we’ll be sitting down on Wednesday, February 26 at 12:00 PM Pacific time. If time zones have got you down, we have a handy time zone converter.
Our Hack Chats are live community events in the Hackaday.io Hack Chat group messaging. This week we’ll be sitting down on Wednesday, February 26 at 12:00 PM Pacific time. If time zones have got you down, we have a handy time zone converter.
Click that speech bubble to the right, and you’ll be taken directly to the Hack Chat group on Hackaday.io. You don’t have to wait until Wednesday; join whenever you want and you can see what the community is talking about. Continue reading “Hacking USB Hack Chat”