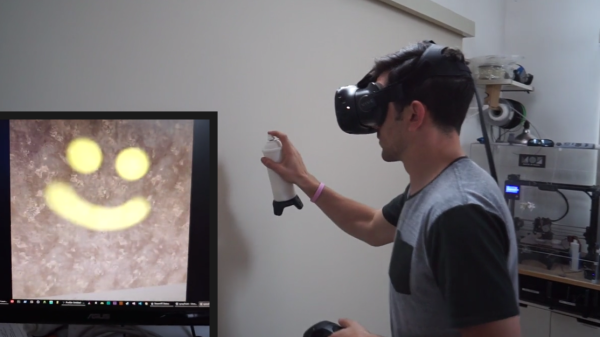
We love a bit of reverse engineering here at Hackaday, figuring out how a device works from the way it communicates with the world. This project from [Jim Yang] is a great example of this: he reverse-engineered the Samsung Gear VR controller that accompanies the Gear VR add-on for their phones. By digging into the APK that links the device to the phone, he was able to figure out the details of the Bluetooth connection that the app uses to connect to the device. Specifically, he was able to find the commands that were used to get the device to send data, and was able to read this data to determine the state of the device. He was then able to use this to create his own web app to use this data.
Continue reading “Reverse Engineering Opens Up The Samsung Gear VR Controller”