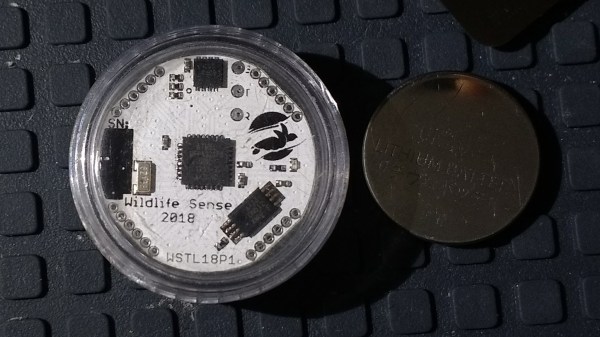
Hacking and tinkering are always fun and games, but one just has to appreciate when all efforts are additionally aimed towards doing something good. [Nikos] sets an example by combining his interest in technology with his passion for wildlife conservation by creating a low cost and ultra-low power temperature logger — and he is using a coin cell for it.
As the founder of a sea turtle conservation project in Greece, [Nikos] enjoys building scientific instruments that help him and his team on their mission. With a goal to log the temperature every 10 minutes over a period of at least 180 days, he designed a PCB just big enough to hold a CR2032 coin cell. Fifty of them will eventually be sealed in waterproof enclosures, and buried in the sand for the whole research duration.
Limiting the design to its bare necessities, the rest of the PCB is housing a digital temperature sensor, an SPI EEPROM to hold all the recorded sensor values over those 180 days, and an ATmega328PB clocked by a 32.768kHz crystal. Wondering what to do with all the extra, unused pins of the ATmega, [Nikos] simply routed them to be accessible through pin headers, thus turning the data logger alternatively into a coin cell powered development board.
Assuming your logging interval requirements are significantly lower, you might be thrilled to hear that [Nikos] estimates a theoretical 7+ years an average coin cell could power the data logger in sleep mode, which makes him confident to reach the 180 days goal.






![[Isambard Kingdom Brunel], in front of the launching chains for the Great Eastern. [Public domain]](https://hackaday.com/wp-content/uploads/2017/11/ikbrunelchains.jpg?w=261)