Counterfeit parts are becoming increasingly hard to tell the difference from the real deal, the technology used by the counterfeiters has come on leaps and bounds, so even the experts struggle to tell the real product from a good fake. Mere fake branding isn’t the biggest problem with a counterfeit though, as ieee.com reports, counterfeit parts could contain malware or be downright dangerous.
Way back in 2014 the FBI charged [Marc Heera] with selling clones of the Hondata S300, a plugin engine module for Honda cars that reads sensors, and depending on their values can change idle speed, air-fuel mixture and a plethora of other car/engine related settings. What, might you ask, is the problem, except they are obviously not genuine parts? According to Honda they had a number of issues such as random limits on engine rpm and occasionally failure to start. While the fake Hondata S300 parts where just poor clones that looked the part, anything connected to an engine control unit brings up huge safety concerns and researchers have shown that through ECU access, they could hijack a car’s steering and brakes.
It’s not just car parts being cloned, remember the fake USB-to-serial chips of FTDI-Gate? Entire routers are also being cloned, which doesn’t sound too bad until you realise that the cloners could configure your internet traffic to be redirected through their network for snooping. In 2010 Saudi citizen [Ehab Ashoor] was convicted of buying cloned Cisco Systems gigabit interface converters with the intention of selling them to the U.S Dept of Defense. While nothing sinister was afoot in [Ashoor]’s case other than greed, these routers were to be deployed in Iraq for use by the Marine Corps networks. They were then to be used for security, transmitting troop movements and relaying intelligence from field operations back to HQ.
So who are the cloners and why are they doing it? It is speculated that some of them may be state funded, as there are a lot of countries who do not trust American silicon. Circuits are reverse engineered and find their way to the international market. Then just like the FTDI-Gate case, cloners want to make profits from others intellectual property. This also brings up another question, if there is a mistrust of American silicon, nearly everything is made in China these days so why should we trust anything from there? Even analog circuits can be made to spy on you, as you can see from the piece we recently featured on compromising a processor using an analog charge pump. If you want to defend yourself from such attacks, perhaps look at previous Hackaday Prize finalist, ChipWhisperer.

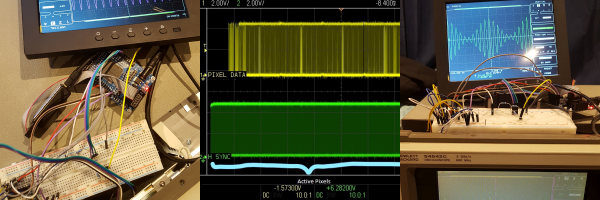




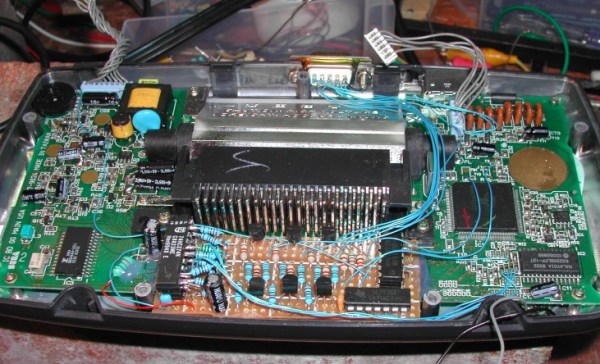
 [EvilTim] first designed a circuit using discrete ’74 series logic which would convert the LCD drive signals to SCART RGB. Of note is the construction technique used in this circuit. A tower of three 74HC374 chips allows [EvilTim] to create R, G, and B outputs without the need for a complex circuit board.
[EvilTim] first designed a circuit using discrete ’74 series logic which would convert the LCD drive signals to SCART RGB. Of note is the construction technique used in this circuit. A tower of three 74HC374 chips allows [EvilTim] to create R, G, and B outputs without the need for a complex circuit board.








