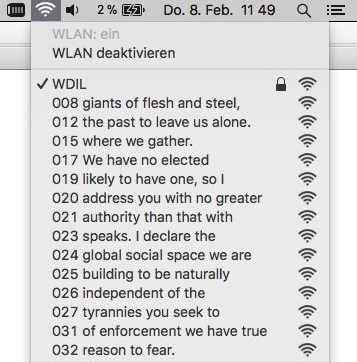
We talk a lot about information security around here, but in reality it’s not at the forefront of everyone’s minds. Most people are content to walk around with their phones constantly looking for WiFi or Bluetooth connections despite the dangers. But if you’re not a black hat sort of person, you can do something like [Verkehrsrot] did and use all of these phones to do something useful and harmless.
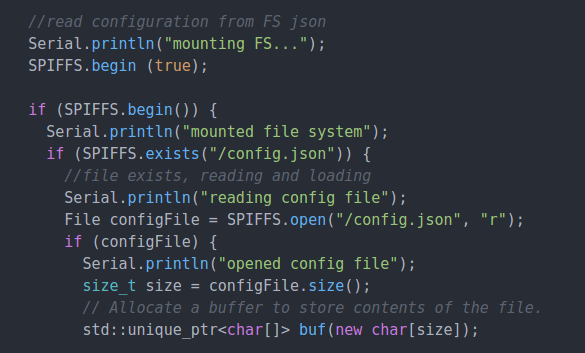
[Verkehrsrot]’s project involves building a radio listening device in order to get an estimate of the amount of traffic in a particular area. The device polls for and detects WiFi and Bluetooth devices nearby and tallies them. For the privacy-minded, it doesn’t persistently store any information about the people or the devices that it detects. The project also runs on a variety of platforms, although you can get the whole thing up and running with little more than an ESP32 and a small lithium-ion battery.
If you’re looking for a useful way to tally the number of people in a given area, this project could be the thing for you. Not everyone keeps their WiFi and Bluetooth turned on, but even so this is still a good way to estimate. But if you need to count everyone going into a room, for example, you’ll need another way to count them.