A lot of us will use satellite communications without thinking much about the satellite itself. It’s tempting to imagine that up there in orbit is a communications hub and distribution node of breathtaking complexity and ingenuity, but it might come as a surprise to some people that most communications satellites are simple transponders. They listen on one frequency band, and shift what they hear to another upon which they rebroadcast it.
This simplicity is not without weakness, for example the phenomenon of satellite hijacking has a history stretching back decades. In the 1980s for example there were stories abroad of illicit trans-atlantic serial links nestling as unobtrusive single carriers among the broad swathe of a broadcast satellite TX carrier.
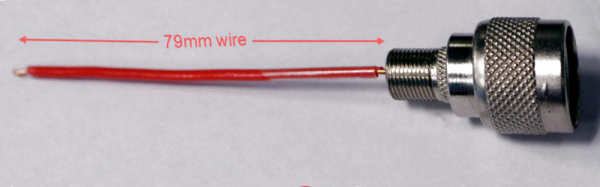
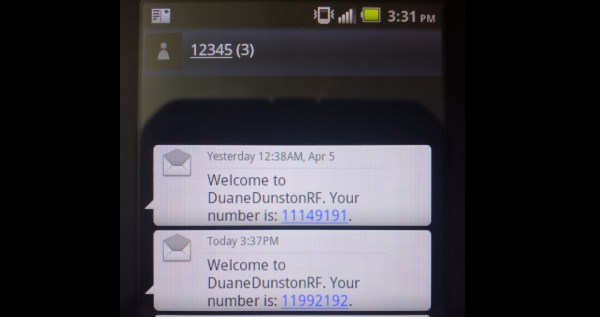
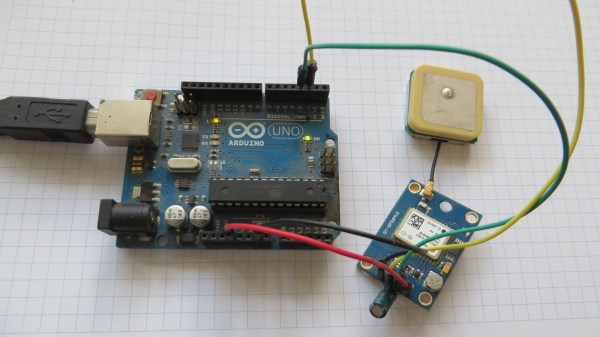
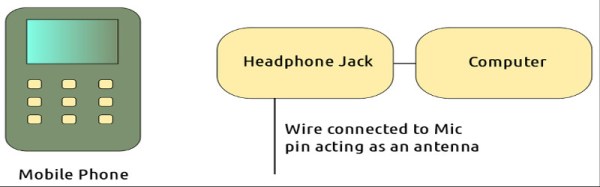
Just sometimes, this phenomenon happens unintentionally. Our attention was drawn to a piece by [Harald Welte] on the unintended rebroadcast of GSM base station traffic over a satellite transponder, and of particular interest is the presentation from a conference in 2012 that it links to. The engineers show how they identified their interference as GSM by its timing frames, and then how they narrowed down its source to Nigeria. This didn’t give them the uplink in question though, for that they had to make a downconverter from an LNB, the output of which they coupled to an aged Nokia mobile phone with a wire antenna placed into an RF connector. The Nokia was able to decode the cell tower identification data, allowing them to home in on the culprit.
There was no fault on the part of the GSM operator, instead an unterminated port on the uplink equipment was enough to pick up the GSM signal and introduce it into the transponder as a parasitic signal for the whole of Europe and Africa to hear. Meanwhile the tale of how the engineers identified it contains enough detective work and outright hardware hacking that we’re sure the Hackaday readership will find it of interest.
If satellite hacks interest you, how about reading our thread of posts on the recapture of ISEE-3, or maybe you’d like to listen for a lost satellite from the 1960s.
Thanks [Kia] for the tip.