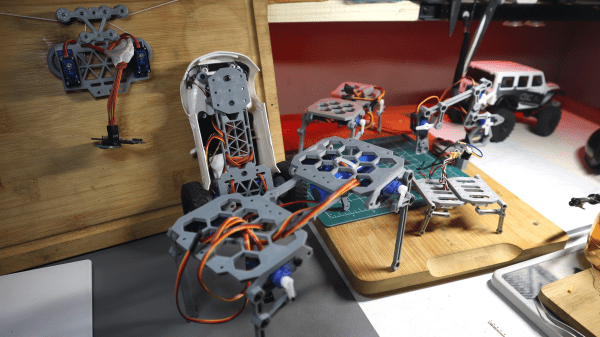
This Hackaday prize entry from [saul] is the beginning of a reconfigurable kit of 3D printed parts and servo motors for robotics learning. With just access to a printer, a few cheap-as-chips servo motors, an Arduino, and some nuts and bolts, you could be hacking together robot walkers within a few hours of starting!
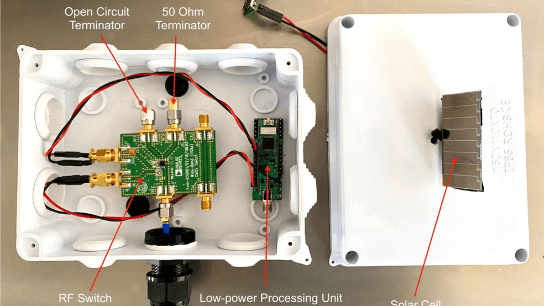
Bolt Bots is very simple to understand, with all the mechanics and wiring out there in the breeze, but strictly for indoor use we reckon. If you want to add remote control to your application, then drop in one of the ubiquitous nRF24L01 boards and build yourself a copy of the remote control [saul] handily provides in this other project.
nRF24L01 boards and build yourself a copy of the remote control [saul] handily provides in this other project.
There really isn’t a great deal we can say about this, as it’s essentially a build kit with quite a few configuration options, and you just have to build with it and see what’s possible. We expect the number of parts to proliferate over time giving even more options. So far [saul] demonstrates a few flavors of ‘walkers’, a rudimentary ‘robot arm’, and even a hanging drawbot.
The bolt hardware can be found in this GitHub repo, and the remote control code in this second one.
Servo-based designs are sometimes sneered at due to their dubious accuracy and repeatability, but with a little of effort, this can be vastly improved upon. Also, multi-legged walkers need multiple servos and controllers to drive ’em. Or do they?
Continue reading “Hackaday Prize 2023: Bolt Bot Micro Servo Droids”