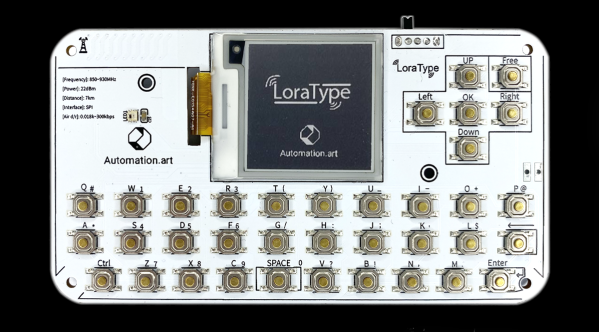
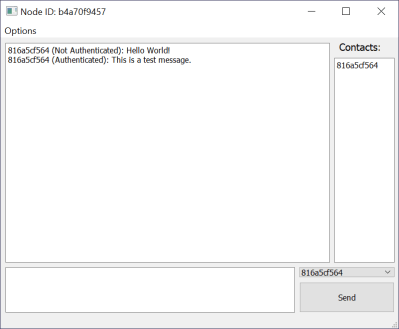
Almost all of modern society is built around various infrastructure, whether that’s for electricity, water and sewer, transportation, or even communication. These vast networks aren’t immune from failure though, and at least as far as communication goes, plenty will reach for a radio of some sort to communicate when Internet or phone services are lacking. It turns out that certain LoRa devices are excellent for local communication as well, and this system known as LoraType looks to create off-grid text-based communications networks wherever they might be needed.
The project is based around the ESP32 platform with an E22 LoRa module built-in to allow it to operate within its UHF bands. It also includes a USB-based battery charger for its small battery, an e-paper display module to display the text messages without consuming too much power, and a keyboard layout for quickly typing messages. The device firmware lets it be largely automated; it will seek out other devices on the local mesh network automatically and the user can immediately begin communicating with other devices on that network as soon as it connects.
There are a few other upsides of using a device like this. Since it doesn’t require any existing communications infrastructure to function, it can be used wherever there are no other easy options, such as in the wilderness, during civil unrest where the common infrastructure has been shut down, or simply for local groups which do not have access to cell networks or Internet. LoRa is a powerful tool for these use cases, and it’s even possible to network together larger base stations to extend the range of devices like these.


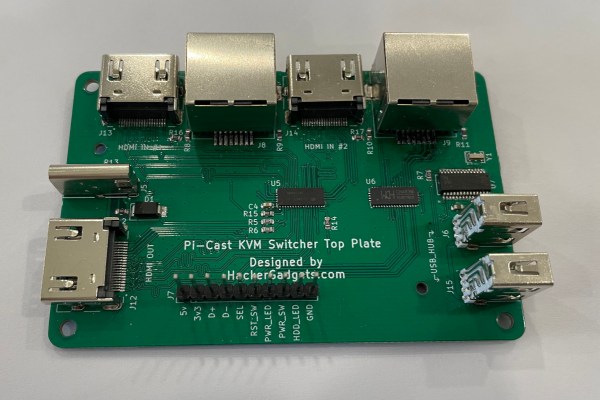


 making uploading firmware a breeze. To that end, a USB port is also provided, hooked up to the uC with the cheap CP2102 USB bridge chip as per most Arduino-like designs. The thing that makes this build a little unusual is the ethernet port. The hardware side of things is taken care of with the
making uploading firmware a breeze. To that end, a USB port is also provided, hooked up to the uC with the cheap CP2102 USB bridge chip as per most Arduino-like designs. The thing that makes this build a little unusual is the ethernet port. The hardware side of things is taken care of with the