We could watch cellphone teardown videos all day long. There’s something pleasing about seeing how everything is packed into such a small enclosure. From the connectors, to that insidious glue, to the minuscule screws, [Scotty Allen] has a real knack for giving us a great look at the teardown process. Take a look at his latest video which attempts to add wireless charging to an iPhone. I think there’s a lot to be said for superb lighting and a formidable camera, but part of this is framing the shots just right.
Now of course we’ve taken apart our fair share of phones and there’s always that queasy “I think I’m going to break something” feeling while doing it. It’s reassuring that [Scotty] isn’t able to do things perfectly either (although he has the benefit of walking the markets for quick replacement parts). This video is a pretty honest recounting of many things going wrong.
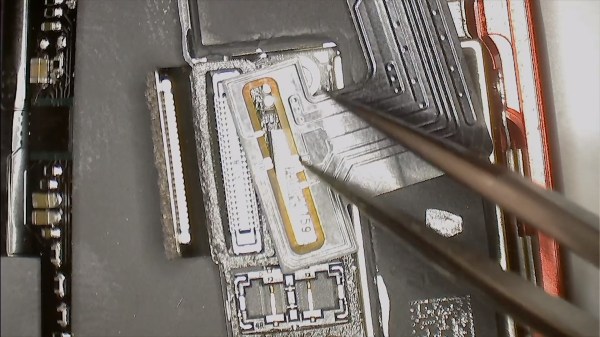
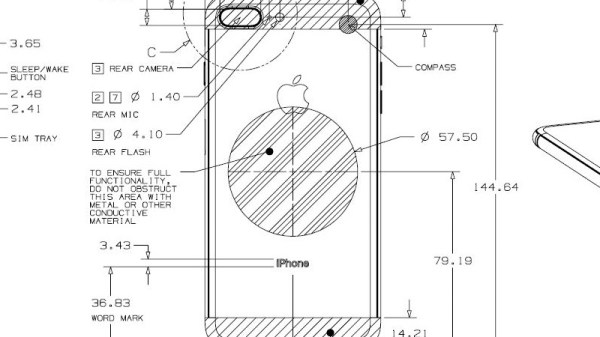
The iPhone 6 and 7 are not meant to have wireless charging, but [Scotty’s] working with a friend named [Yeke] who created an aftermarket kit for this. The flexible PCB needs to be folded just right, and adhesive foam added (along with a magical incantation) to make it work. That’s because the add-on is a no-solder job. Above you can see it cleverly encircles one of the mating connectors and relies on mechanical pressure to make contact with the legs of that connector. Neat!
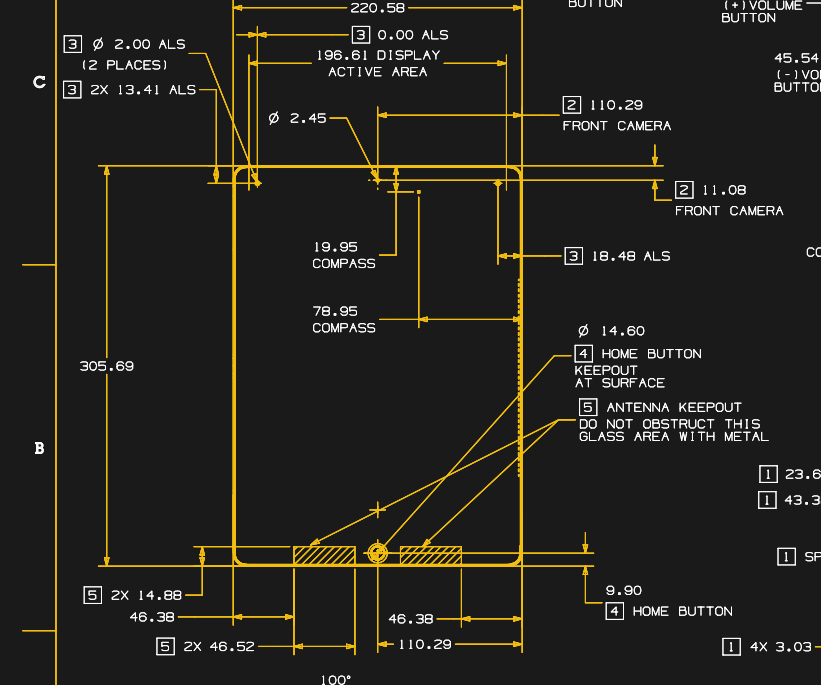
In the second half of the video [Scotty] meets up with [Yeke] to discuss the design itself. We find it interesting that [Yeke] considers his work a DIY item. Perhaps it’s merely lost in translation, but perhaps [Yeke’s] proximity to multiple flexible PCB manufacturers makes him feel that this is more like playing around for fun than product design. Any way you look at it, the ability to design something that will fit inside that crazy-tight iPhone case is both impressive and mesmerizing. Having seen some of the inductive charging hacks over the years, this is by far the cleanest way to go about it.
We caught up with [Scotty] during last year’s Supercon. We may not be able to drop everything and move to Shenzhen, but hearing about the experience is just enough to keep us wanting to!
Continue reading “You Can Add Wireless Charging To IPhone… Kinda”



 This comes to our attention because [Pablo] referenced it to modify an
This comes to our attention because [Pablo] referenced it to modify an