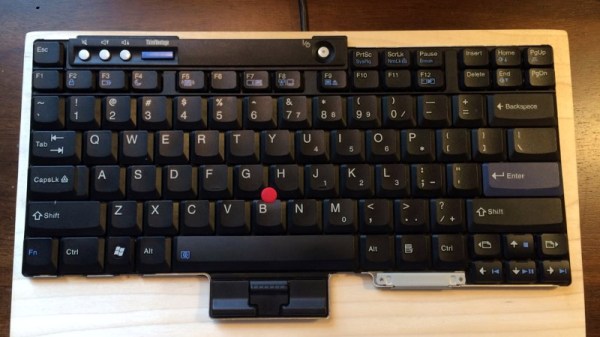
[Frank Adams] liked the keyboard on his Lenovo ThinkPad T61 so much that he decided to design an adapter so he could use it over USB with the Teensy microcontroller. He got the Trackpoint working, and along the way managed to add support for a number of other laptop boards as well. Before you know it, he had a full-blown open source project on his hands. Those projects can sneak up on you when you least expect it…
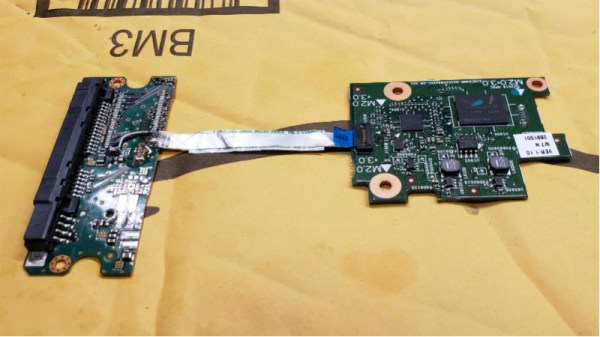
 The first step of the process is getting your laptop keyboard of choice connected up to the Teensy, but as you might expect, that’s often easier said than done. They generally use a flexible printed circuit (FPC) “ribbon cable” of some type, but may also be terminated in any number of weirdo connectors. [Frank] goes over the finer points of getting these various keyboards connected to his PCB, from searching the usual suspects such as Aliexpress and Digikey for the proper connector to throwing caution to the wind and cutting off problematic nubs and tabs to make it fit.
The first step of the process is getting your laptop keyboard of choice connected up to the Teensy, but as you might expect, that’s often easier said than done. They generally use a flexible printed circuit (FPC) “ribbon cable” of some type, but may also be terminated in any number of weirdo connectors. [Frank] goes over the finer points of getting these various keyboards connected to his PCB, from searching the usual suspects such as Aliexpress and Digikey for the proper connector to throwing caution to the wind and cutting off problematic nubs and tabs to make it fit.
You might be on your own for figuring out the best way to connect your liberated keyboard up, but [Frank] has done his part by designing a few PCBs which handle routing the appropriate connections to the Teensy LC or 3.2 microcontroller. He’s such a swell guy he’s even written the firmware for you. As of right now there’s currently a dozen keyboards supported by his software and hardware setup, but he also gives tips on how to get the firmware modified for your own board if you need to.
It should come as no surprise that it was a Thinkpad keyboard that got [Frank] going down this path; as we’ve documented over the years, hackers love their Thinkpads. From fitting them with more modern motherboards to going full on matryoshka and putting a second computer inside of one, it’s truly the laptop that launched a thousand hacks.