Drivers with a lead foot more often than not have Waze open on their phone so they can see if other drivers have spotted cops up ahead. But avoiding a speeding ticket used to involve a lot more hardware than software. Back before the smartphone revolution, that same driver would have had a radar detector on their dashboard. That’s not to say the gadgets are completely unused today, but between their relatively high cost (one of the top rated models on Amazon as of this writing costs over $300) and the inevitable false positives from so many vehicles on the road having their own radar and LIDAR systems, they’ve certainly become a less common sight over the years
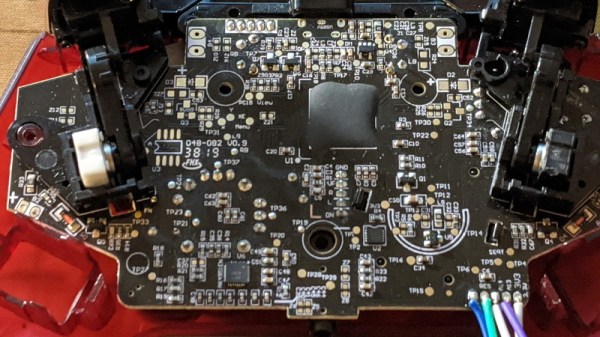
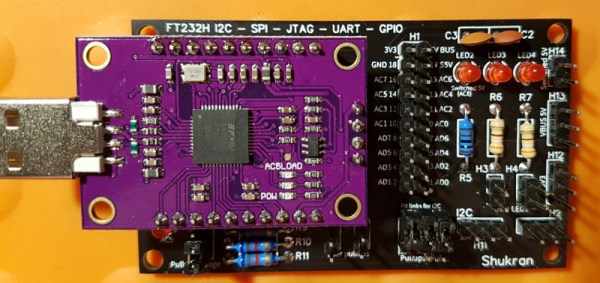
The subject of today’s teardown is a perfect example of “Peak Radar Detector”. Manufactured back in 2007, the Cobra XRS 9740 would have been a fairly mid-range entry offering the sort of features that would have been desirable at the time. Over a decade ago, having an alphanumeric display, voice alerts, and a digital compass were all things worth shouting about on the box the thing was sold in. Though looking like some kind of Cardassian warship was apparently just an added bonus.
As the name implies these devices are primarily for detecting radar activity, but by this point they’d also been expanded to pick up infrared lasers and the strobe beacons on emergency vehicles. But false positives were always a problem, so the device allows the user to select which signals it should be on the lookout for. If you were getting some kind of interference that convinced the detector it was being bombarded with IR lasers, you could just turn that function off without having to pull the plug entirely.
But it’s important to remember that this device was built back when people were still unironically carrying around flip phones. Detecting laser and multi-band radars might sound like something pulled from the spec sheet of a stealth fighter jet, but this is still a piece of consumer electronics from more than a decade in the past. So let’s crack it open and take a look at what goes on inside a radar detector that’s only a few years away from being old enough to get its own driver’s license.



 The
The