In the maker world, it’s the Arduino and ESP32 lines that get the lion’s share of attention. However, you can do fantastic things with PIC chips, too, if you put the dev time in—it’s just perhaps less likely another maker has done so before you. A great example is this VGA output project from [grecotron].
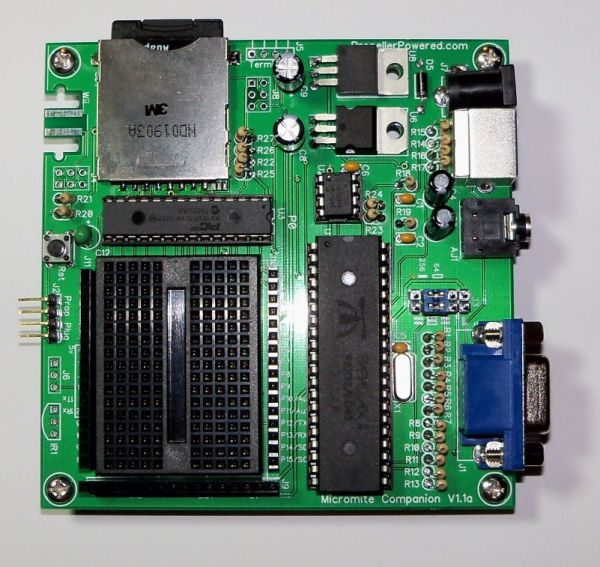
A PIC18F47K42 is perhaps not the first part you would reach for to pursue any sort of video-based project. However, with the right techniques, you can get the 8-bit microcontroller pumping out the pixels surprisingly well. [grecotron] was able to get the chip outputting to a VGA monitor at a resolution of 360 x 480 with up to 16 colors. It took some careful coding to ensure the chip could reliably meet the timing requirements for the standard and to get HSYNC, VSYNC, and the color signals all dancing in harmony. Aiding in this regard was that the chip was clocked with a 14.3182 MHz crystal to make it easy to divide down from all the internal timers as needed. Supporting hardware is light, too—primarily consisting of a VGA connector, a couple of multiplexers, and resistor ladder DACs for the color signals. Files are on Github for those interested in deeper detail on the work.
VGA output is possible to implement on all kinds of microcontrollers—and even a bunch of raw logic if you know what you’re doing. If you’re pursuing your own video output wizardry, be sure to let us know on the tipsline.