As the saying goes, there’s no lock that can’t be picked, much like there’s no networked computer that can’t be accessed. It’s usually a continual arms race between attackers and defenders — but for some modern passenger vehicles, which are essentially highly mobile computers now, the defenders seem to be asleep at the wheel. The computing systems that control these cars can be relatively easy to break into thanks to manufacturers’ insistence on using wireless technology to unlock or activate them.
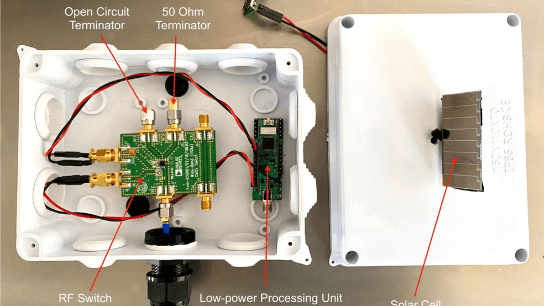
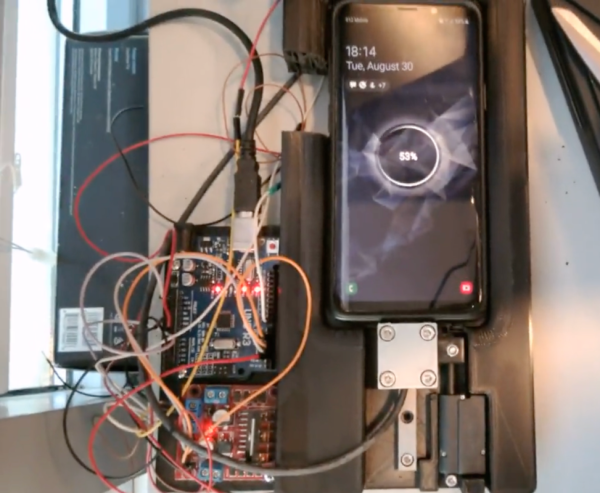
This particular vulnerability involves the use of a piece of software called gattacker which exploits vulnerabilities in Bluetooth Low Energy (BLE), a common protocol not only for IoT devices but also to interface a driver’s smartphone or other wireless key with the vehicle’s security system. By using a man-in-the-middle attack the protocol between the phone and the car can be duplicated and the doors unlocked. Not only that, but this can be done without being physically close to the car as long as a network of some sort is available.
[Kevin2600] successfully performed these attacks on a Tesla Model 3 and a few other vehicles using the seven-year-old gattacker software and methods first discovered by security researcher [Martin Herfurt]. Some other vehicles seem to have patched these vulnerabilities as well, and [Kevin2600] didn’t have universal success with every vehicle, but it does remind us of some other vehicle-based attacks we’ve seen before.